More than 14,000 instances of F5 BIG-IP APM are still exposed to RCE attacks

Non-profit cyber threat monitoring firm Shadowserver has found more than 14,000 instances of APM’s BIG-IP exposed online during ongoing attacks exploiting remote control code extraction (RCE) vulnerabilities.
BIG-IP APM (short for Access Policy Manager) is F5’s centralized access management proxy solution designed to help administrators secure access to their organizations’ networks, cloud, applications, and application programming interfaces (APIs).
This 5-month-old bug (tracked as CVE-2025-53521) was disclosed in October as a denial-of-service (DoS) vulnerability and reclassified as an RCE bug over the weekend.
“Due to new information discovered in March 2026, the original vulnerability is being reclassified to RCE. An original CVE fix is warranted to address RCE in fixed versions. We have learned that this vulnerability has been exploited in vulnerable versions of BIG-IP,” warned F5 in an advisory update on Sunday.
Unprivileged attackers exploit this security issue to gain remote code execution on unpublished BIG-IP APM systems that have access policies configured on the virtual server.
While there is no information on how many BIG-IP APM instances have been exposed online with compromised configurations, nonprofit cyber threat monitoring firm Shadowserver said Wednesday it is tracking more than 17,100 IPs with BIG-IP APM fingerprints.
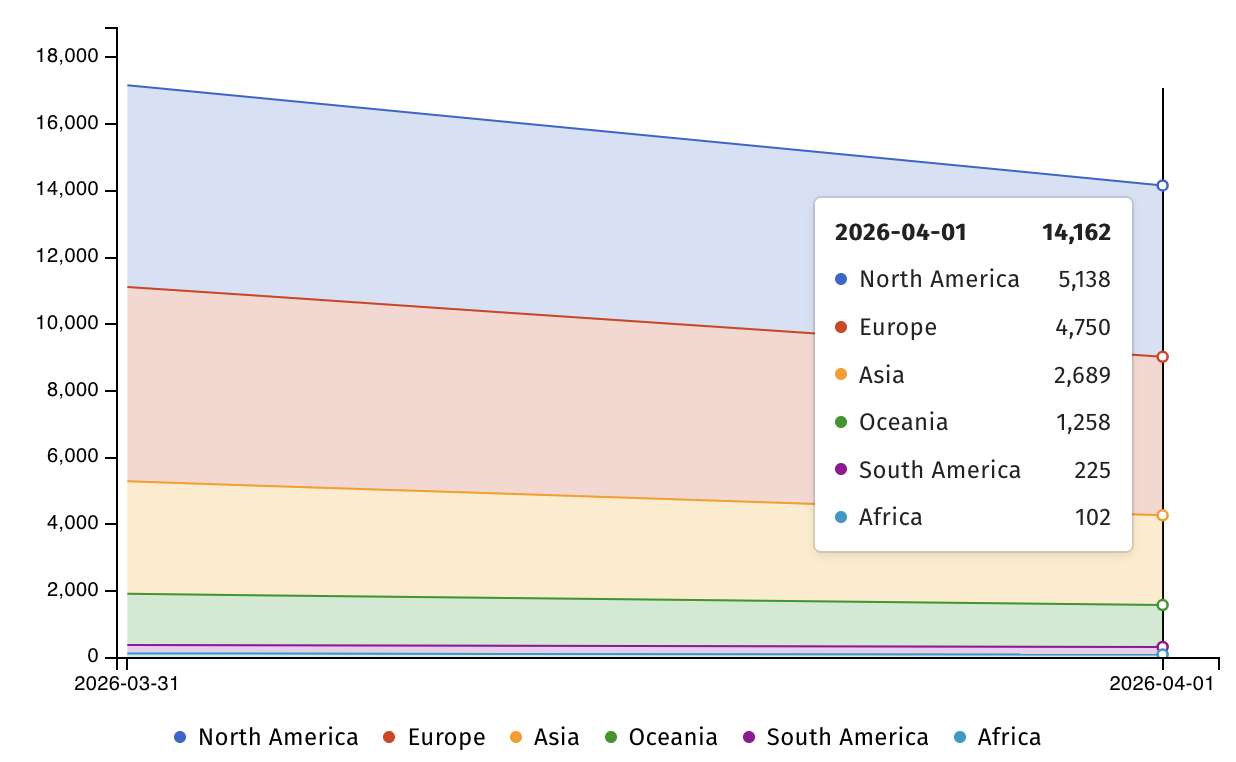
More than 14,000 BIG-IP APM systems are still exposed to the CVE-2025-53521 attack according to Shadowserver data, even though the US Cybersecurity and Infrastructure Security Agency (CISA) ordered government agencies to secure their BIG-IP APM systems by midnight Monday (after adding the existing vulnerability to its list).
F5 also shares published indicators of compliance (IOCs) and advises defenders to examine disks, logs, and terminal history of BIG-IP devices for signs of malicious activity. It also provides guidance on steps to take after finding evidence of a compromise, including rebuilding affected systems from scratch.
“If customers don’t know exactly when a system has been compromised, backups of the user configuration set (UCS) may have been created after that happened,” the company said.
“F5 strongly recommends that customers rebuild the configuration from a known good source because UCS files from compromised systems can contain persistent malware.”
As a Fortune 500 technology giant, F5 provides cybersecurity, application delivery networking (ADN), and other services to more than 23,000 customers, including 48 Fortune 50 companies.
In recent years, BIG-IP vulnerabilities have been targeted by both state agencies and cybercrime groups to breach corporate networks, hijack devices, deliver data-wiping malware, map internal servers, and steal sensitive data.

Automatic logging proves that the path exists. BAS proves that your controls are stopping you. Many teams run without each other.
This white paper outlines six areas of validation, indicates where coverage ends, and provides clinicians with three diagnostic questions for any screening tool.



