Vercel confirms the breach as criminals say they are selling the stolen data

Cloud development platform Vercel disclosed a security breach after malicious actors claimed to have breached its systems and attempted to sell the stolen data.
Vercel is a cloud platform that provides hosting and deployment infrastructure for developers, specializing in JavaScript frameworks.
The company is known for building Next.js, the widely used React framework, and providing services such as serverless operations, edge computing, and CI/CD pipelines that allow developers to build, preview, and release applications.

In a security report published today, the company said a small percentage of customers were affected by the security breach.
“We have identified a security incident involving unauthorized access to certain Vercel internal systems,” Vercel warned.
“We are investigating further, and have contacted incident response specialists to assist in the investigation and corrections. We have notified law enforcement and will update this page as the investigation continues.”
The company says its services have not been affected and it is working with affected customers.
Vercel says it is taking steps to protect its customers, advising them to update location variables, use its sensitive location variable feature, and rotate secrets if necessary.
Hacker claims to sell stolen Vercel data
The disclosure comes after the “ShinyHunters” threat actor posted on a hacking forum that they had breached Vercel and were selling access to the company’s data.
It should be noted that while the hacker claimed to be part of the ShinyHunters gang, the terror actors associated with the latest attack attributed to the ShinyHunters gang denied BleepingComputer any involvement in the incident.
In a forum post, the hacker said he was selling access keys, source code, and database data allegedly stolen from Vercel, as well as access to internal implementations and API keys.
“This is from Linear as proof, but the access I’m going to provide includes multiple employee accounts with access to multiple internal implementations, API keys (including NPM tokens and other GitHub tokens),” the forum post reads.
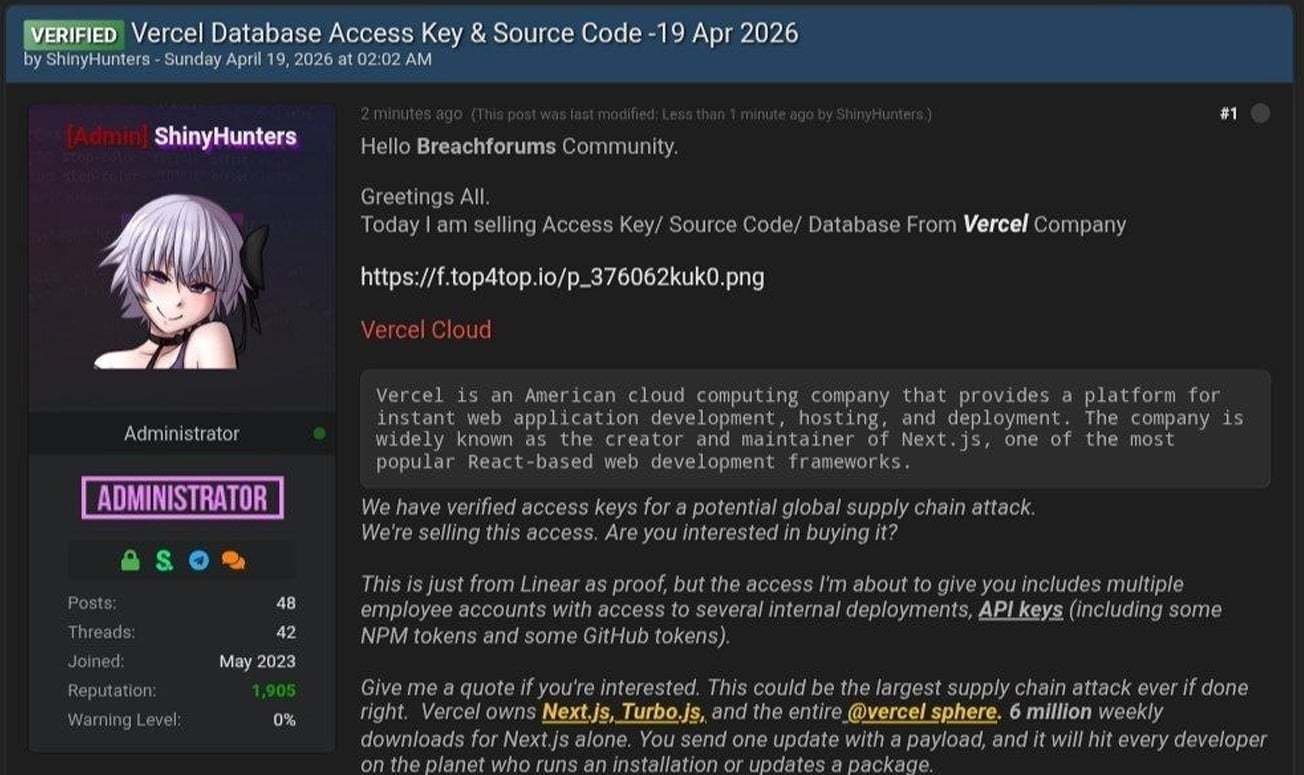
The attacker also shared a text file containing Vercel employee information, which included 580 data records containing names, Vercel email addresses, account status, and job timestamps. They also shared a screenshot of what appears to be Vercel Enterprise’s internal dashboard.
BleepingComputer could not independently verify if the data or screenshot is authentic.
In the messages shared on Telegram, the fearsome actor also said that they have been in contact with Vercel regarding the incident and that they have discussed the alleged ransom demand of $2 million.
BleepingComputer has contacted Vercel with additional questions about the breach, including whether any sensitive data or credentials were exposed and if they are interviewing the attackers, and we will update this story when we hear back.

AI has tied four zero days to a single exploit that bypasses both renderer and OS sandboxes. A wave of new exploits is coming.
At the Automated Validation Conference (May 12 & 14), see how autonomous, context-rich validation finds usability, validates controls, and closes the correction loop.