The new Microsoft Defender “RedSun” zero-day PoC grants SYSTEM privileges

A researcher known as “Chaotic Eclipse” published the exploit of Microsoft Defender zero-day evidence, called “RedSun,” two weeks ago, contradicting the way the company works with cybersecurity investigators.
This exploit is a local privilege elevation (LPE) flaw that grants SYSTEM privileges in Windows 10, Windows 11, and Windows Server in the latest April Patch Tuesday patches, when Windows Defender is enabled.
“When Windows Defender realizes that a malicious file has a cloud tag, for whatever stupid and ridiculous reason, the antivirus it’s supposed to protect decides it’s a good idea to rewrite the file it found and back to its original location,” explains the researcher.

“PoC exploits this behavior to overwrite system files and gain administrative privileges.”
Will Dormann, principal risk analyst at Tharros, confirmed to BleepingComputer that the new Microsoft Defender RedSun exploit is active and gives full SYSTEM privileges on Windows 10, Windows 11, and Windows Server 2019 and later.
“This Exploit uses the ‘Cloud Files API’, writes EICAR to a file using it, uses an oplock to win a volume shadow copy race, and uses a directory junction to redirect the overwritten file (with new content) to C:Windowssystem32TieringEngineService.exe,” Dormann wrote in Marston’s thread.
“Currently, the Cloud Files Infrastructure is using the attacker-planted TieringEngineService.exe (which is RedSun.exe self-service) as SYSTEM. Game over.”
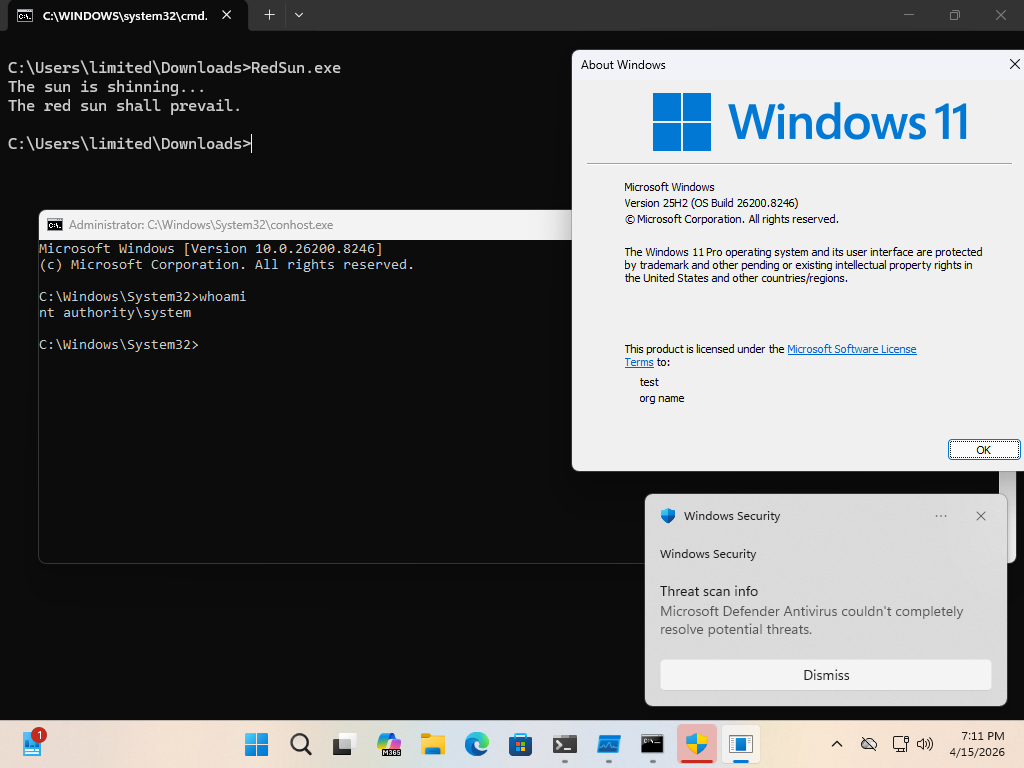
Source: Dormann
Dormann says that some antivirus vendors on VirusTotal are getting exploits [VirusTotal] because the executable contains an embedded EIRCAR (antivirus check file). However, he reduced the adoption [VirusTotal] by encoding the EICAR string inside the executable.
A more detailed whitepaper about this vulnerability was shared by security researcher Kevlar.
Last week, this researcher, known as “Chaotic Eclipse,” released a Microsoft Defender LPE zero-day exploit, called “BlueHammer,” which is now tracked as CVE-2026-33825. Microsoft fixed the bug as part of this month’s Patch Tuesday security updates.
The researcher says they published both zero-day PoCs protesting how Microsoft works with cybersecurity researchers who disclose vulnerabilities to the Microsoft Security Response Center (MSRC).
“Normally, I would have made a plan and begged them to fix the problem but let me sum it up. I was told by them that they will ruin my life and they did that and I don’t know if I am the only one who has this problem or if there are only a few people who have faced this problem but I think most of them would just eat it and cut their losses but for me they took everything,” said the researcher.
“They messed with me and pulled all the childish games they could. It got so bad at one point I wondered if I was working with a big company or someone who was happy to see me suffer but it seems to be a collective decision.”
BleepingComputer contacted the researcher for more details on their collaboration with the MSRC.
When contacting Microsoft about these alleged issues, they shared the following statement.
“Microsoft is committed to customers’ commitment to investigating reported security issues and updating affected devices to protect customers as quickly as possible,” a Microsoft spokesperson told BleepingComputer.
“We also support systematic vulnerability disclosure, a widely accepted industry practice that helps ensure issues are thoroughly investigated and resolved before public disclosure, which supports both customer protection and the security research community.”

AI has tied four zero days to a single exploit that bypasses both renderer and OS sandboxes. A wave of new exploits is coming.
At the Automated Validation Conference (May 12 & 14), see how autonomous, context-rich validation finds usability, validates controls, and closes the correction loop.