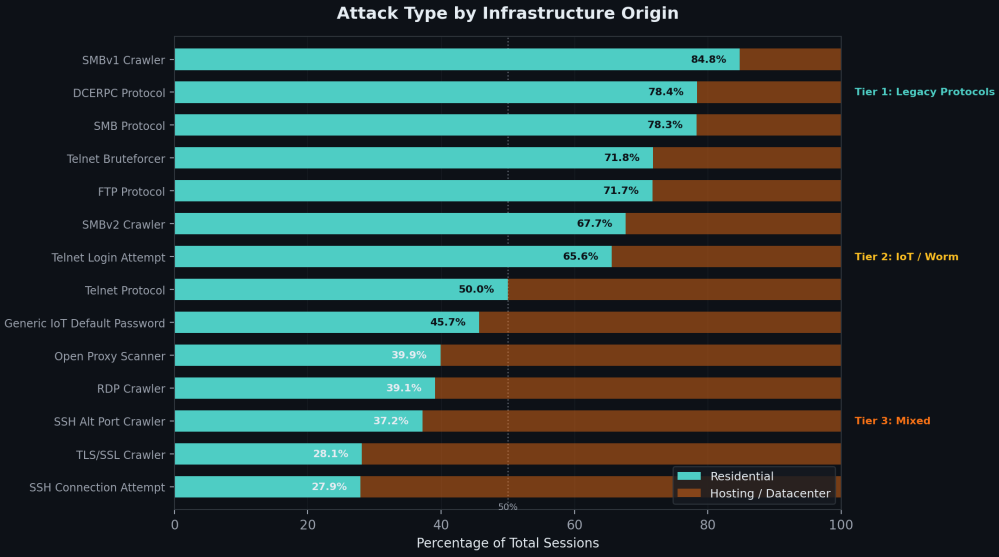
Residential attorneys avoided IP reputation testing in 78% of 4B cases

Researchers warn that residential proxies used to route malicious traffic are a major problem for IP reputation systems, as there is no clear distinction between attackers and legitimate users.
This happens because proxies are very short-lived, passive, or systematically rotated, preventing security systems from cataloging them in time.
Cybersecurity intelligence platform GreyNoise determined this after analyzing a massive dataset of 4 billion malicious edge-targeting sessions over a three-month period.
About 39% of those times appear to be from home networks, certainly part of residential proxies, but 78% of them are not visible from reputable feeds.
“The data reveals a pattern that challenges a key assumption of network security: that you can tell attackers from legitimate users where the traffic is coming from,” explained GreyNoise.
According to the company, many residential IPs are used once or twice, then disappear, and attackers rotate them with others, which keeps the speed at a level that shadow programs will not mark.
About 89.7% of resident IPs work in violent activities for less than a month, while only 8.7% last for 2 months, and 1.6% persist for 3 months.
Those that are kept alive for a long time seem to hold a special hold according to the researchers, with a focus on SSH and using Linux TCP stacks.
Source: GreyNoise
Diversity is another factor that makes it difficult to flag and block, as GreyNoise data shows the residential IPs participating in the attacks belong to 683 Internet service providers.
Another reason for their stealth is that they are used for network scanning and retesting, with only 0.1% involved in actual operations, the researchers said.
A small percentage (1.3%) targeted corporate VPN business login pages, while a limited number of cases also involved routing IP addresses and authentication attempts.
Regarding the source of residential proxies, GreyNoise says that China, India, and Brazil are the main contributors, as traffic from IPs follows people’s sleep patterns, dropping by a third at night, when most people turn off their devices.
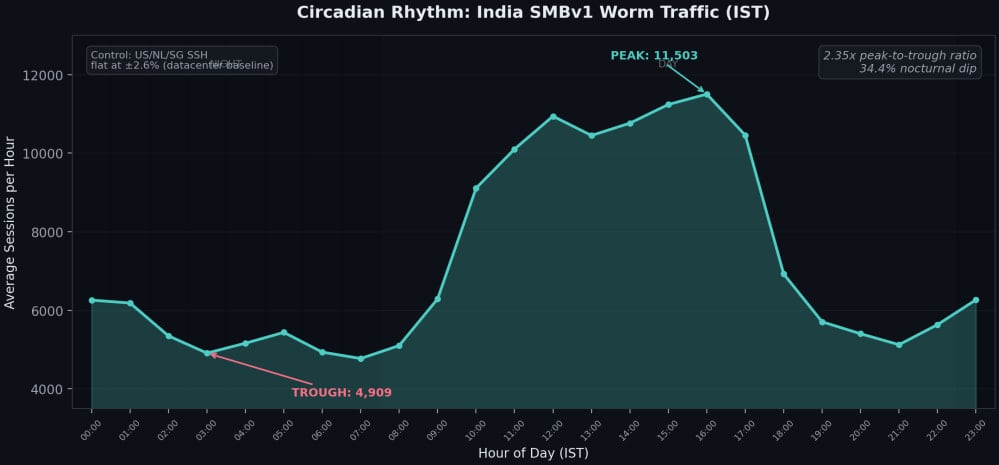
Source: GreyNoise
The researchers report that residential proxy traffic is generated by two separate, non-overlapping ecosystems: IoT botnets and infected computers.
In cases involving the latter, proxies appear in SDKs for free VPNs, ad blockers, and similar applications, which register users’ devices in bandwidth sales programs.
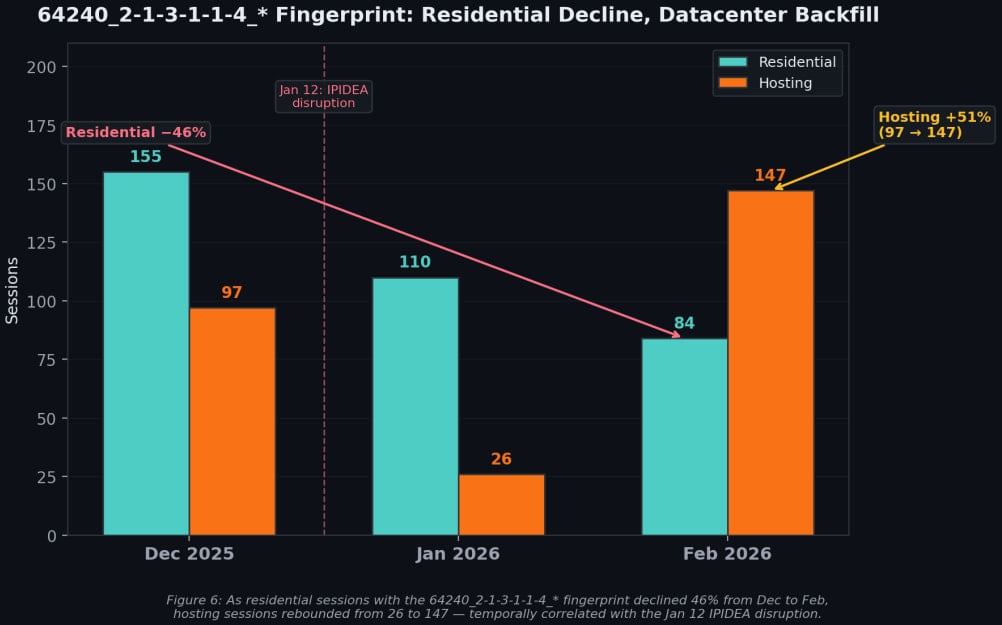
GreyNoise also highlighted the resilience of these networks using the example of IPIDEA, one of the largest residential proxy networks in the world, which was recently disrupted by Google Threat Intelligence Group (GTIG) and partners.
The disruption reduced its proxy pool by about 40%, but in the following period, the traffic of the datacenter increased, indicating that the demand can be absorbed by others when necessary and that the lost capacity is quickly replaced.
Source: GreyNoise
GreyNoise argues that strategies to evade public service need to abandon IP reputation as a primary signal and instead focus on behavior.
The researchers propose to find a sequence check on the rotating residential IPs, to block illegal protocols like SMB in the ISP space, and to trace the fingerprint of the device that survives the IP rotation.

Automatic logging proves that the path exists. BAS proves that your controls are stopping you. Many teams run without each other.
This white paper outlines six areas of validation, indicates where coverage ends, and provides clinicians with three diagnostic questions for any screening tool.