Russia Is Behind Latest TP-Link Router Hack, According to UK’s Cyber Security Agency

The UK’s National Cyber Security Center (NCSC) has warned companies and government agencies that Russian hackers are conducting a vicious campaign to steal passwords and data by targeting TP-Link routers, the Register reports. Perhaps this is part of why TP-Link and other “foreign-made” routers were recently banned from being imported into the United States.
The NCSC report highlights the Russian hacking group APT28, also known as Fancy Bear, which has been linked to the Russian Intelligence Service, the GRU. They have been targeting security actions on small and home routers and changing their DNS settings to redirect victims to malicious websites they control, to continue exploiting targets and spreading damaging malware.
The attack appears to be aimed at exploiting Ukrainian infrastructure, and the hacker group is reportedly targeting niche MikroTik routers, many of which are located in Ukraine. Risking it would give Russia information or access to infrastructure that could affect its military objectives through its illegal invasion of Ukraine.
“This work shows how exploitable vulnerabilities in widely used network devices can be developed by malicious actors,” said Paul Chicheter, director of operations at NCSC. “We strongly encourage organizations and network defenders to familiarize themselves with the strategies described in the advisory and follow mitigation advice.”
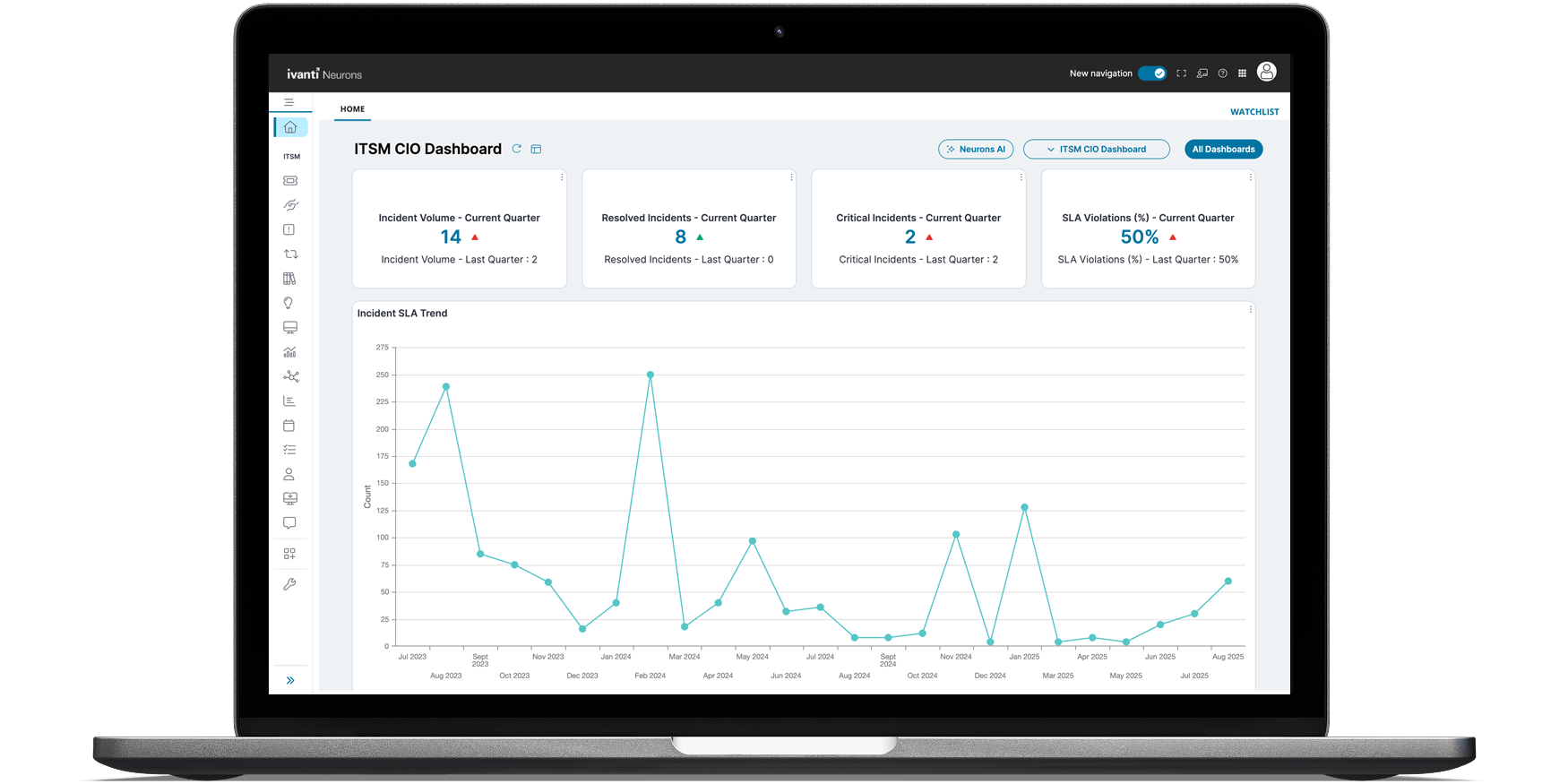
Microsoft published an explanation of how the attack worked.
Credit: Microsoft
Microsoft has been tracking and mitigating exploit activity. In its report, it revealed that Russian hacking groups have been targeting TP-Link and similar router products since August 2025. It shows that the attacks were mainly designed to gain access to upstream organizations, which groups can use to reach other better monitored or protected locations.
“Forest Blizzard, which primarily collects intelligence in support of the Russian government’s foreign policy initiatives, also used its DNS hijacking functionality to support an attack in the middle (AiTM) on Transport Layer Security (TLS) connections against Microsoft Outlook web domains,” Microsoft explained. It noted that this could allow Russian hacking groups to intercept cloud data, potentially leaving critical institutions such as the government, energy sector, and telecommunications infrastructure vulnerable.
Microsoft software and fake Microsoft services were key elements in this attack. Microsoft noted that fake versions of its Outlook website were being used to trick users, and that Russian groups were targeting Microsoft-owned servers to try to get hold of sensitive corporate data.
Microsoft and NCSC encourage organizations to exercise caution in analyzing their DNS traffic for suspicious activity. Malicious domains should also be blocked directly to prevent the spread of malicious code, and most importantly, we should not use home router solutions in business environments where additional security may be required.