European Commission hack exposes data of 30 EU organisations

The European Union’s Cybersecurity Service (CERT-EU) revealed that the hacking of the European Commission’s cloud by the TeamPCP threat group, said that the breach caused exposed the information of at least 29 other organizations of the Union.
The European Commission publicly disclosed the incident on March 27 after BleepingComputer received confirmation that the Amazon cloud environment of the European Union’s largest organization had been breached.
Two days earlier, the Commission notified CERT-EU of the hack, saying that the Cybersecurity Operations Center was not informed of the misuse of the API, the possible corruption of the account, or any unusual network traffic until March 24, five days after the first entry.
On March 10, TeamPCP used an Amazon Web Services API key with administrative rights over some European Commission AWS accounts (stolen in the Trivy supply-chain attack) to breach the Commission’s Amazon environment.
In the next stage of the attack, they used TruffleHog (a cloud credential scanning and verification tool) to search for additional secrets, then attached a newly generated access key to an existing user to avoid detection before performing further checks and stealing data.
TeamPCP has been linked to supply-chain attacks targeting many other developer code platforms, such as GitHub, PyPi, NPM, and Docker.
A cybercriminal group compromised the LiteLLM PyPI package in an attack that affected tens of thousands of devices using the “TeamPCP Cloud Stealer” information-stealing malware.
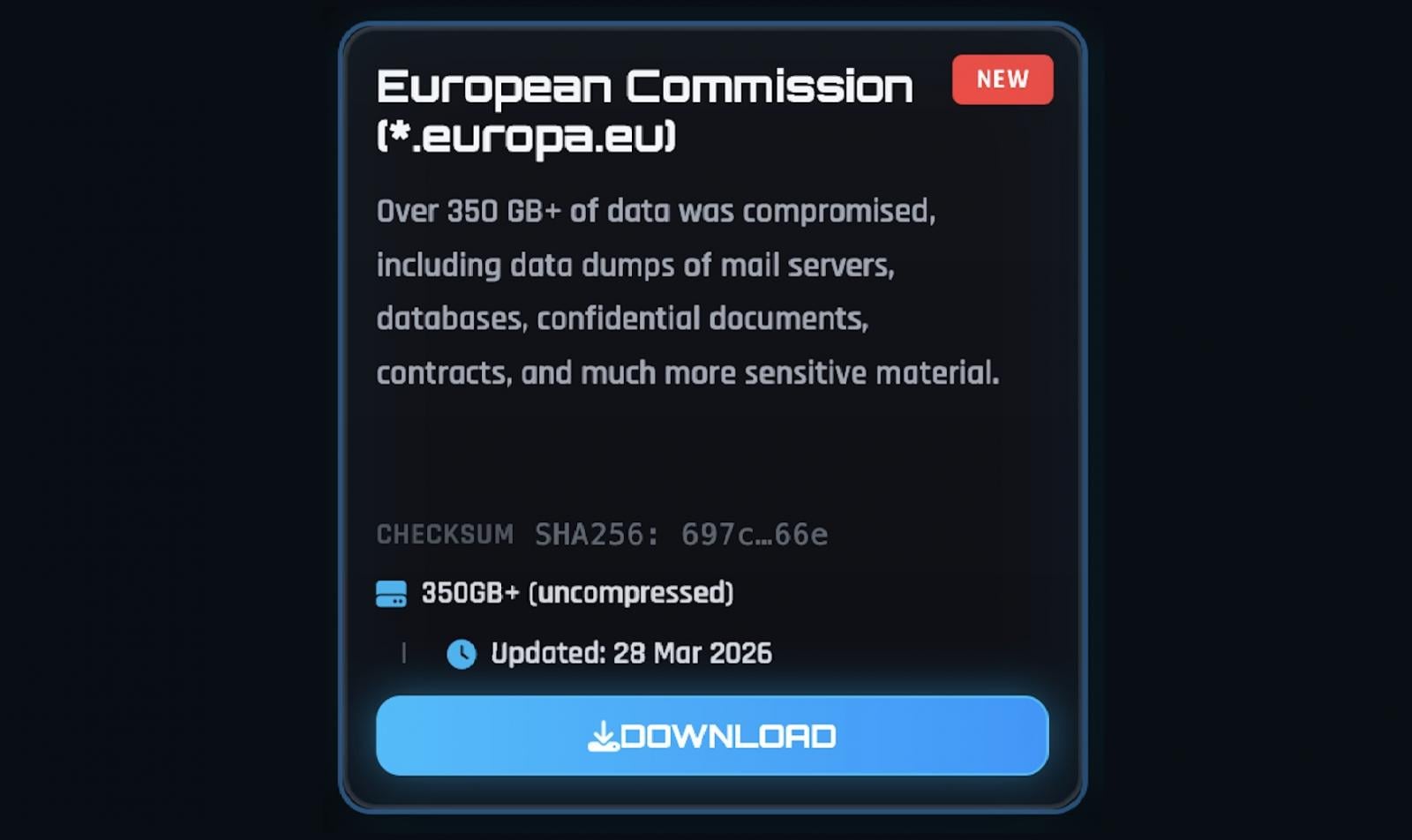
The data was leaked on the dark web by ShinyHunters
On March 28, the phishing group ShinyHunters published the stolen dataset on their dark web leak as an archive of 90GB of documents (about 340GB uncompressed), containing names, email addresses, and email content.
CERT-EU’s analysis confirmed that threat actors have stolen tens of thousands of files containing personal information, usernames, email addresses, and email content, and that the result of the data breach may affect at least 42 customers of the European Commission and 29 other Union organizations that use the europa.eu web hosting service.
“A threat actor used a vulnerable AWS password to extract data from the affected cloud area. The filtered data is related to websites hosted by up to 71 clients of the Europa web hosting service: 42 internal clients of the European Commission, and at least 29 other Union organizations,” said CERT-EU on Thursday.
“The analysis of the dataset published so far has confirmed the existence of personal data, including lists of names, surnames, usernames, and email addresses, mainly from the websites of the European Commission but possibly concerning users across many Union organizations,” it added.
“The dataset contains at least 51,992 files related to outgoing e-mail communications, amounting to 2.22 GB. Most of them are automatic notifications with little or no content. However, ‘bounce back’ notifications, which are responses to incoming messages from users, may contain content originally sent by the user, which poses a risk of personal data exposure.”
CERT-EU added that no websites were taken offline as a result of the incident or disrupted, and no movement to other Commission AWS accounts was detected.
Although the analysis of the generated databases and files is ongoing and will require “a long period of time,” the Commission has notified the relevant data protection authorities and is in direct contact with the organizations concerned.
In February, the European Commission disclosed another data breach after discovering that a mobile device management platform used to manage employees’ devices had been hacked.

Automatic logging proves that the path exists. BAS proves that your controls are stopping you. Many teams run without each other.
This white paper outlines six areas of validation, indicates where coverage ends, and provides clinicians with three diagnostic questions for any screening tool.