FBI takedown of W3LL phishing service leads to developer arrest

The FBI’s Atlanta Field Office and Indonesian authorities have dismantled the global “W3LL” phishing network, seizing infrastructure and arresting the developer in what is described as the first joint enforcement action between the United States and Indonesia targeting a developer of the phishing kit.
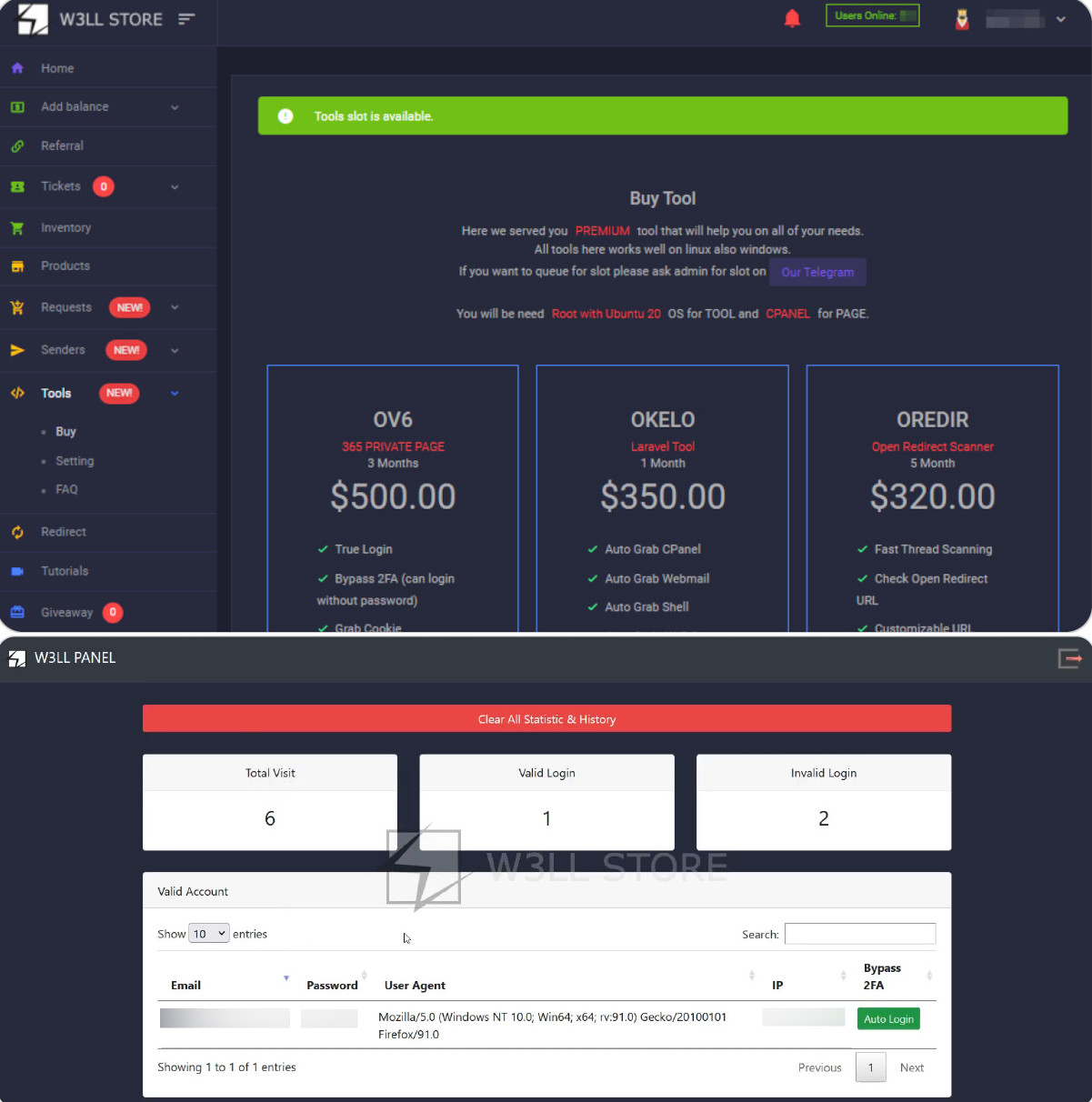
The W3ll Store was a phishing kit and online marketplace that allowed hackers to steal thousands of credentials and attempt to defraud over $20 million.
“This Website has been seized as part of an enforcement action taken against the W3LL STORE,” reads a message from the w3ll host.[.]store website.

“The w3ll.store domain was seized by the Federal Bureau of Investigation pursuant to a warrant issued pursuant to 18 USC §§ 981 and 982 by the United States District Court for the Northern District of Georgia as part of a joint law enforcement action by the Federal Bureau of Investigation.”

Source: BleepingComputer
The W3LL phishing kit sold for $500 and allowed attackers to create convincing imitations of corporate logins in order to gain credentials. The kit allowed malicious actors to capture authentication session tokens, allowing attackers to bypass multi-factor authentication and gain access to compromised accounts.
Source: Group-IB
The threat actor also offered a marketplace called W3LLSTORE, where stolen information and unauthorized network access were bought and sold.
“This wasn’t just a phishing attack—it was a full-blown cybercrime,” said FBI Special Agent in Charge Marlo Graham.
Authorities say the marketplace facilitated the sale of more than 25,000 compromised accounts between 2019 and 2023, and even after W3LLSTORE was shut down, the operation continued through encrypted messaging platforms, where the toolkit was rebranded and sold to other threat actors.
Between 2023 and 2024, the phishing kit was used to target more than 17,000 victims worldwide, and investigators discovered that the developer collected and resold access to compromised accounts.
The W3LL phishing platform was previously linked to campaigns targeting corporate Microsoft 365 accounts and was designed to support business email (BEC) attacks from initial access through post-exploitation.
The phishing kit relies on adversary-in-the-middle attacks, where login portals are authenticated through the attacker’s infrastructure.
This allows malicious actors to monitor and intercept credentials, one-time MFA passcodes, and real-time cookies. These session cookies may be used to log into compromised accounts without triggering MFA authentication challenges.
Once access is gained, attackers will monitor inboxes, create email rules, and impersonate victims to commit invoice fraud and redirect payments to BEC attacks.

Automatic logging proves that the path exists. BAS proves that your controls are stopping you. Many teams run without each other.
This white paper outlines six areas of validation, indicates where coverage ends, and provides clinicians with three diagnostic questions for any screening tool.