Firestarter malware survives Cisco firewall updates, security patches

Cybersecurity agencies in the US and UK are warning about a malware called Firestarter that is running on Cisco Firepower and Secure Firewall devices that use the Adaptive Security Appliance (ASA) or Firepower Threat Defense (FTD) software.
The backdoor is said to have been created by a threat actor that Cisco Talos tracked inside as UAT-4356, known for cyberespionage campaigns, including ArcaneDoor.
The Cybersecurity and Infrastructure Security Agency (CISA) and the UK National Cyber Security Center (NCSC) believe that the adversary gained initial access by exploiting a missing authorization issue (CVE-2025-20333) and/or a buffer overflow bug (CVE-2025-20362).

In one incident at a public administration branch office, CISA observed a threat actor first deploying the Line Viper malware, a user-mode shellcode loader, and then using Firestarter, which allows continued access even after patching.
“CISA has not yet confirmed the exact date of the first exploit but is evaluating the regression as occurring as early as September 2025, even before the agency applies patches in accordance with ED 25-03,” the agency notes in the alert.
Line Viper is used to establish VPN sessions and access all configuration information, including administrative credentials, certificates, and private keys on vulnerable Firepower devices.
Next, ELF’s Firestarter backdoor binary is used for persistence, allowing a threat actor to regain access when needed.
Once Firestarter is installed on devices, it maintains persistence across reboots, firmware updates, and security patches. In addition, the backdoor automatically restarts when terminated.
Persistence is achieved by connecting to LINA, the core process of the Cisco ASA, and using signal handlers that trigger reset methods.
A joint malware analysis report from two cybersecurity agencies explains that Firestarter modifies the boot/mount’s CSP_MOUNT_LIST file to ensure startup, saves a copy of it to /opt/cisco/platform/logs/var/log/svc_samcore.log, and returns it to /usr/bin/linacs, in the background.
Cisco Talos also published its analysis of the malware, saying that the persistence mechanism is triggered when a process termination signal is received, also known as a graceful restart.
The researchers noted in the Firestarter report that the backdoor used the following commands to set itself to persist:
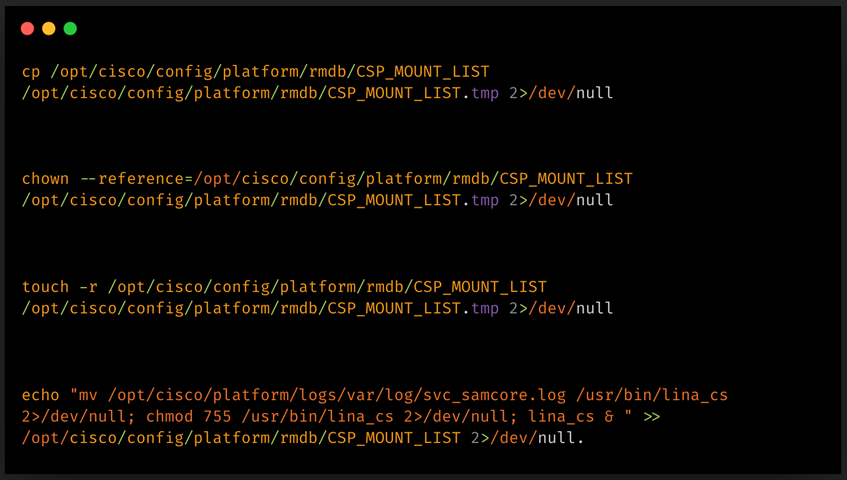
Source: Cisco
The main function of the implant is to act as a back door for remote access, while it can use the shellcode provided by the attacker.
This is done in a way where Firestarter connects to LINA by changing the XML handler and injecting shellcode into memory, creating a controlled execution path.
This shellcode is launched by a specially designed WebVPN application, which, after authenticating a hard-coded identifier, loads and executes attacker-provided payloads directly in memory.
However, CISA did not provide any details on the specific payloads seen in the attack.
Cisco has published security advisories about the Firestarter that contain mitigations and workarounds to remove the persistence method, as well as tips on how to install a Firestarter.
The vendor “strongly recommends refactoring and upgrading the device using a fixed release,” including both compromised and non-compromised cases.
To determine a compromise, administrators must run the ‘show kernel process | enter the lina_cs’ command. For any resulting output, the device should be considered vulnerable.
If rebooting the device isn’t possible yet, Cisco says a cold reboot (powering down the device) removes the malware. However, this alternative method is not recommended as it carries the risk of database or disk corruption, leading to startup problems.
CISA also shares two YARA rules that can detect the Firestarter backdoor when used in a disk image or key dump from a device.

AI has tied four zero days to a single exploit that bypasses both renderer and OS sandboxes. A wave of new exploits is coming.
At the Automated Validation Conference (May 12 & 14), see how autonomous, context-rich validation finds usability, validates controls, and closes the correction loop.
Find Your Place