LinkedIn is privately testing 6,000+ Chrome extensions, collecting data

A new report called “BrowserGate” warns that Microsoft’s LinkedIn uses hidden JavaScript scripts on its website to scan visitors’ browsers for installed extensions and collect device data.
According to a report by Fairlinked eV, which claims to be LinkedIn’s commercial user association, the Microsoft platform injects JavaScript into user sessions that checks thousands of browser extensions and links the results to visible user profiles.
The author says this behavior is used to collect sensitive personal and company information, as LinkedIn accounts are tied to real identities, employers, and job roles.
“LinkedIn tests more than 200 products that compete directly with its marketing tools, including Apollo, Lusha, and ZoomInfo. Because LinkedIn knows each individual employer, it can map which companies are using competing products. It pulls the customer lists of thousands of software companies from their users’ browsers without anyone’s knowledge,” the report said.
“Then it uses what it finds. LinkedIn has already sent enforcement threats to users of third-party tools, using data obtained from these private scans to identify its targets.”
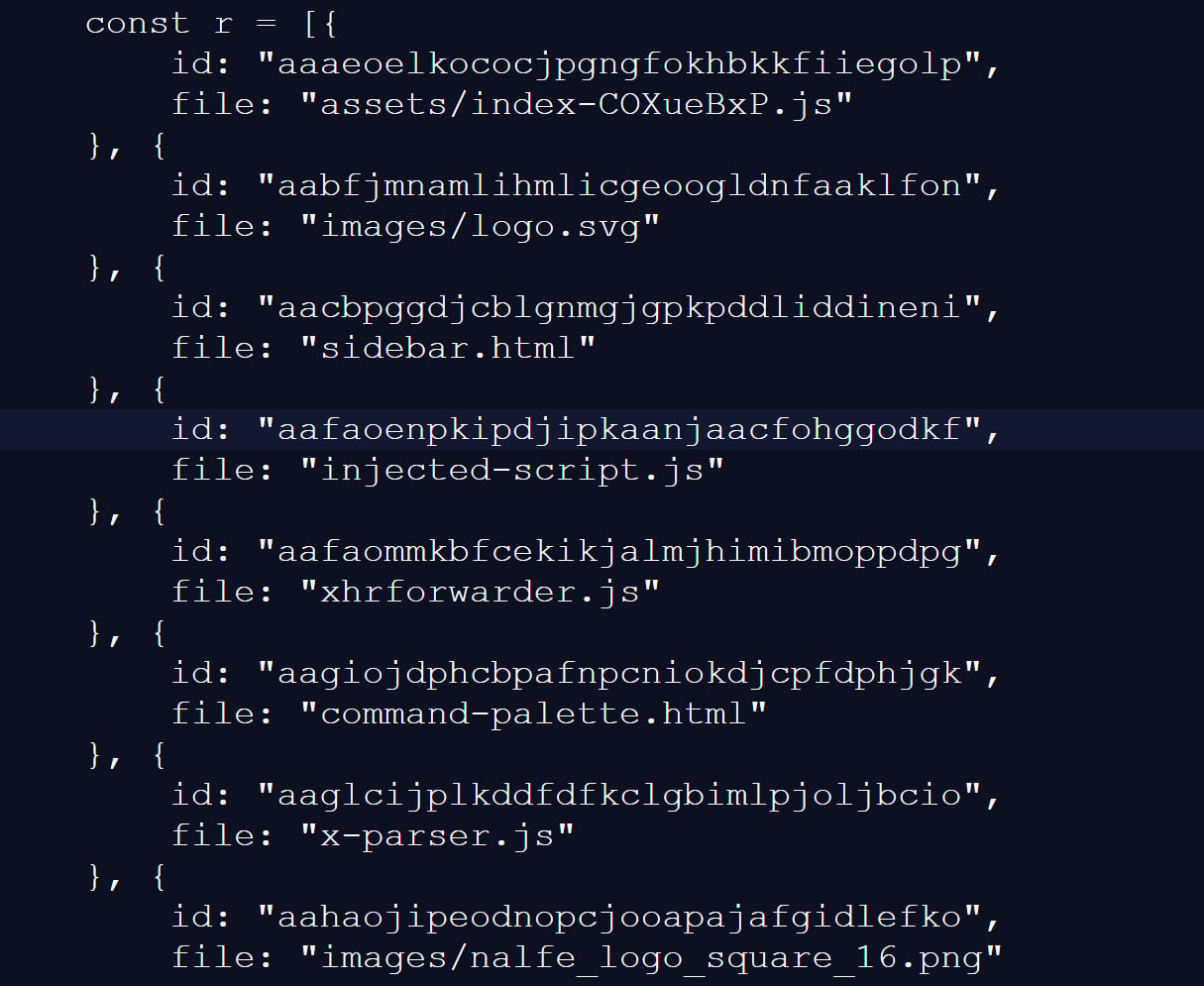
BleepingComputer independently verified part of these claims through our own testing, where we saw a JavaScript file with a random file name being uploaded to LinkedIn’s website.
This script tested 6,236 browser extensions by trying to access the file resources associated with a specific extension ID, a well-known way to determine if extensions are installed.
This fingerprint script was previously reported in 2025, but only received about 2,000 extensions at that time. A separate GitHub site from two months ago shows 3,000 extensions available, indicating that the number of extensions available continues to grow.
Source: BleepingComputer
While most of the scanned extensions are related to LinkedIn, the script also surprisingly detected language and grammar extensions, tax professional tools, and other seemingly unrelated features.
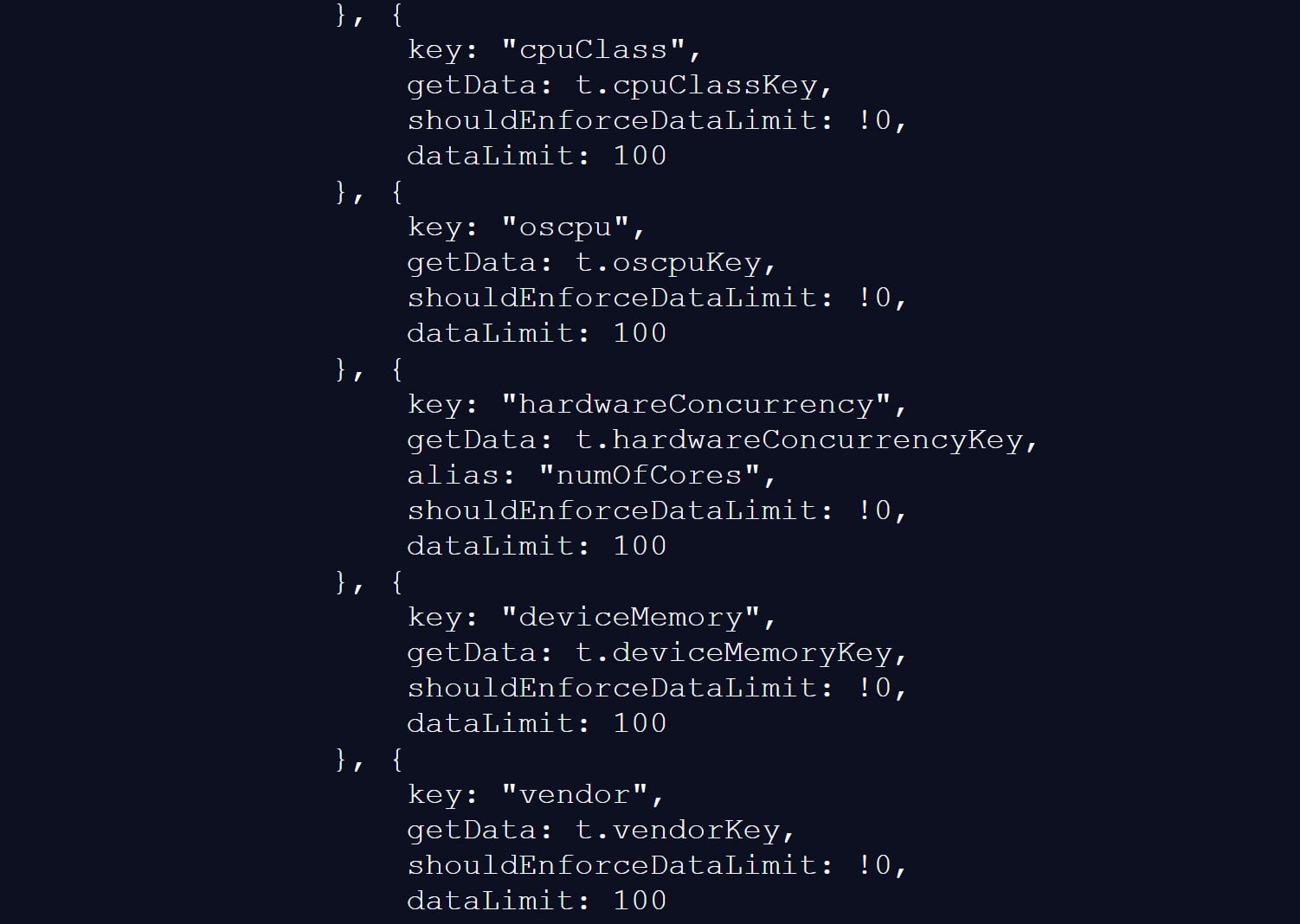
The script also collects a wide range of browser and device data, including critical CPU counts, available memory, screen resolution, time zone, language settings, battery status, audio information, and storage features.
Source: BleepingComputer
BleepingComputer could not verify the claims in the BrowserGate report about data usage or whether it was shared with third parties.
However, similar fingerprinting methods have been used in the past to create unique browser profiles, which would allow tracking users across websites.
LinkedIn denies allegations of data use
LinkedIn does not deny that it receives certain browser extensions, telling BleepingComputer that the information is used to protect the platform and its users.
However, the company says the report comes from someone whose account has been banned for deleting LinkedIn content and violating the site’s terms of use.
“The claims made on the website linked here are completely false. The person behind them is subject to account restrictions for scrubbing and other violations of LinkedIn’s Terms of Service.
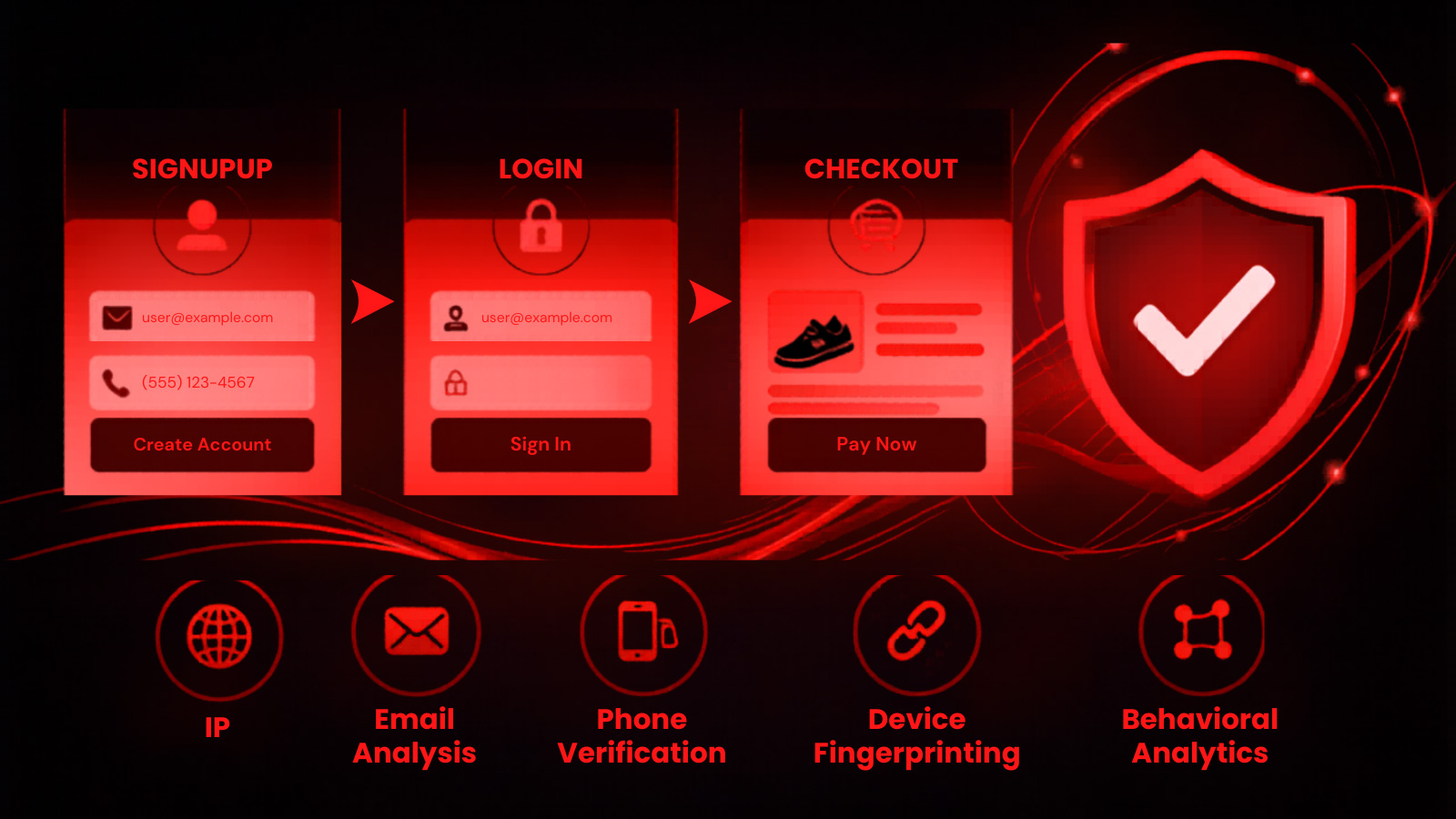
In order to protect the privacy of our members, their data, and to ensure the stability of the site, we check for extensions that extract data without members’ consent or that violate LinkedIn’s Terms of Service.
Here’s the reason: some extensions have static resources (images, javascript) available for embedding in our web pages. We can detect the presence of these extensions by checking if that static resource URL exists. This discovery is visible within the Chrome developer console. We use this data to determine which extensions violate our policies, to inform and improve our technical defenses, and to understand why a member’s account may download a negative amount of other members’ data, which, on average, affects the stability of the site. We do not use this data to consider sensitive information about members.
For more context, in retaliation for this limitation of the website owner’s account, they tried to get an injunction in Germany, saying that LinkedIn violated various laws. The court ruled against them and found that their claims against LinkedIn were unfounded, and in fact, their personal data practices are illegal.
Unfortunately, this is the case of someone who lost in the court of law, but wants to retry the case in the court of public opinion regardless of its accuracy.”
LinkedIn says the BrowserGate report stems from a dispute involving the developer of a LinkedIn-related browser extension called “Teamfluence,” which LinkedIn says violates the platform’s terms of service.
In documents shared with BleepingComputer, a German court rejected the developer’s request for a preliminary injunction, finding that LinkedIn’s actions did not constitute illegal prohibition or discrimination.
The court also found that automated data collection alone could violate LinkedIn’s terms of use and that it had the authority to block accounts to protect its platform.
LinkedIn argues that the BrowserGate report is an attempt to re-litigate that controversy publicly.
Whatever the reasons for the report, one point is indisputable.
The LinkedIn site uses a fingerprinting script that detects more than 6,000 extensions running on the Chromium browser, as well as other data about the visitor’s system.
It’s not the first time that companies have used aggressive fingerprint scripts to find programs running on a visitor’s device.
In 2021, eBay was found to be using JavaScript to perform automatic port scans on visitors’ devices to determine if they were running different support software.
Although eBay never confirmed why they used these scripts, it was widely believed that they were used to prevent fraud on compromised devices.
It was later discovered that many other companies were using the same fingerprint, including Citibank, TD Bank, Ameriprise, Chick-fil-A, Lendup, BeachBody, Equifax IQ connect, TIAA-CREF, Sky, GumTree, and WePay.

Automatic logging proves that the path exists. BAS proves that your controls are stopping you. Many teams run without each other.
This white paper outlines six areas of validation, indicates where coverage ends, and provides clinicians with three diagnostic questions for any screening tool.