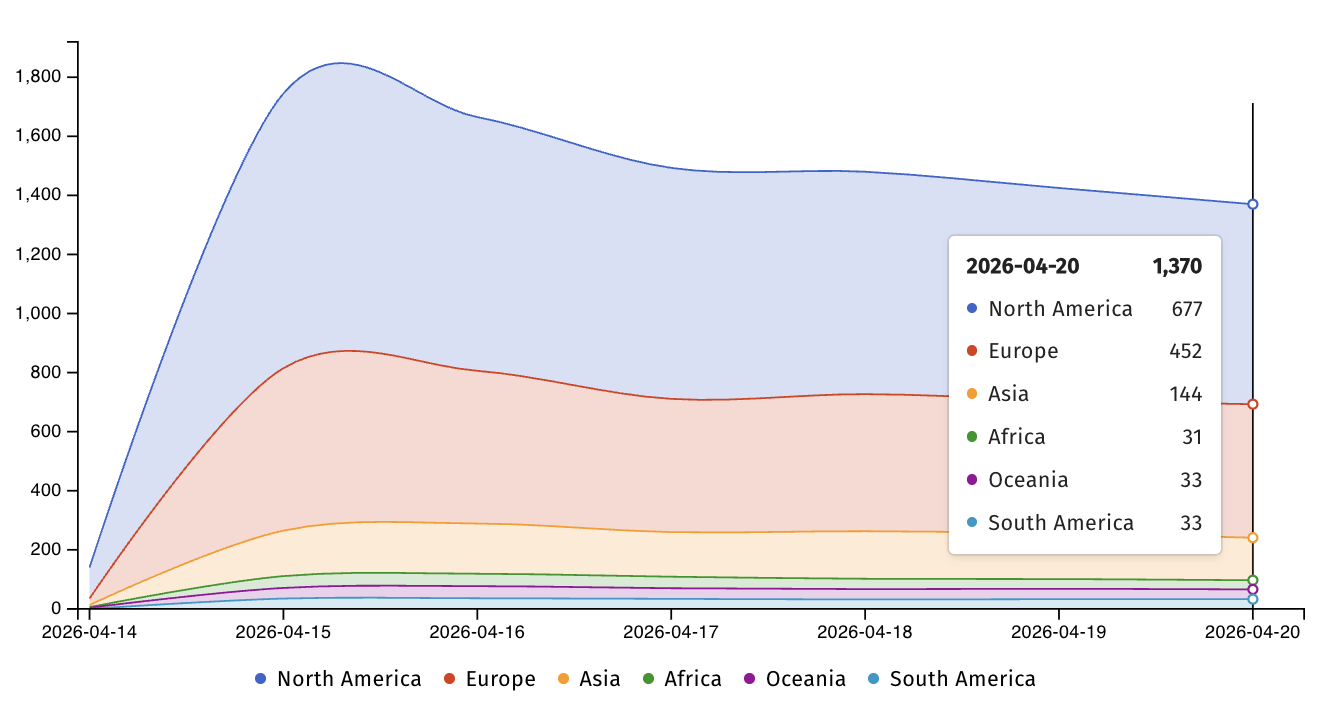
More than 1,300 Microsoft SharePoint servers are vulnerable to phishing attacks

More than 1,300 Microsoft SharePoint servers exposed on the Internet remain unprotected against a spoofing vulnerability that was exploited as a zero-day and is still being exploited in ongoing attacks.
The security flaw, tracked as CVE-2026-32201, affects SharePoint Enterprise Server 2016, SharePoint Server 2019, and SharePoint Server Subscription Edition (the latest on-premises version, which uses the “continuous update” model).
As Microsoft explained when it included this security issue as part of the April 2026 Patch on Tuesday, a successful exploit allows malicious actors without privileges to perform network spoofing by using incorrect input validation weaknesses in sophisticated attacks that do not require user interaction.

“An attacker who successfully exploited the vulnerability may view some sensitive information (Privacy), make changes to the exposed information (Integrity), but cannot restrict access to the device (Discovery),” it said.
Although Microsoft has marked the vulnerability as zero-day, it has not disclosed how it was exploited in the attack or linked the malicious activity to a specific threat actor or hacking group.
On Tuesday, Internet security monitoring group Shadowserver warned that more than 1,300 undocumented Microsoft SharePoint servers exposed on the Internet are still waiting to be protected, with fewer than 200 systems patched since Microsoft issued security updates for CVE-2026-32201 last week.
On the same day Microsoft released patches for CVE-2026-32201, CISA added the vulnerability to its catalog known as Known Exploited Vulnerabilities (KEV).
The US cybersecurity agency also ordered Federal Civilian Executive Branch (FCEB) agencies (agencies that manage non-military branches, such as the Treasury Department and the Department of Homeland Security) to patch SharePoint servers within two weeks, on April 28, as directed by Binding Operational Directive (BOD) 22-01.
“This type of vulnerability is a common attack by malicious actors and poses a significant risk to government business,” it warned.
“Use mitigations in each vendor’s instructions, follow applicable BOD 22-01 guidelines for cloud services, or stop using the product if mitigations are not available.”
One week ago, CISA also raised the alarm about Windows Task Host’s rising vulnerability as it is being exploited in the wild, warning government agencies to secure their devices as quickly as possible, as it could allow attackers to gain SYSTEM privileges on vulnerable devices.
On April 14, Microsoft released security updates that address 167 vulnerabilities, including two zero-day flaws, as part of the April 2026 Patch Tuesday.

AI has tied four zero days to a single exploit that bypasses both renderer and OS sandboxes. A wave of new exploits is coming.
At the Automated Validation Conference (May 12 & 14), see how autonomous, context-rich validation finds usability, validates controls, and closes the correction loop.
Find Your Place