Aikido Security starts with Endpoint security for AI developers

Belgian cybersecurity company Aikido Security BV today introduced Endpoint, a lightweight security agent designed to protect the use of artificial intelligence in developer workplaces and supply chain attacks against open source software.
Endpoint delivers a platform for businesses to gain visibility and control over software packages, independent development environments, browser extensions and AI tools that are now integrated into modern software development.
The company says that engineer workstations and laptops have become blind spots for many organizations. For the most part, these computers and devices are just as secure as any other machine running on a business. Traditional security puts developers through lengthy approval processes – which they then skip – or rely on weak controls that ignore the risks.
AI-driven development and deployment has introduced a variety of new attack surfaces that traditional security has yet to reach. Aikido said Endpoint helps enterprises fully embrace AI-native software development securely and at scale by providing real-time monitoring and policy enforcement, while giving developers flexibility.
That means developers can import tools, packages, Model Context Protocol hooks, extensions, AI tools and agents, while Endpoint checks them before installation.
“Enterprises are distributing AI coding tools to thousands of developers with no visibility and control over what’s actually running on developer workstations,” said co-founder and CEO Willem Delbare. “Our approach to self-protecting software creates the boundaries for this new era of development by protecting not only the code that is deployed, but also the environment in which it is produced.”
Endpoint is built on Aikido Safe Chain, the company’s open source malware detection and protection system, with more than 200,000 downloads every week. It uses a lightweight AI agent that persists across developer environments and runs before any package, IDE, plugin or browser extension is installed. It checks and reports.
As an added security measure, any packages published less than 48 hours ago are automatically intercepted, removing the most vulnerable window for attacks after installation.
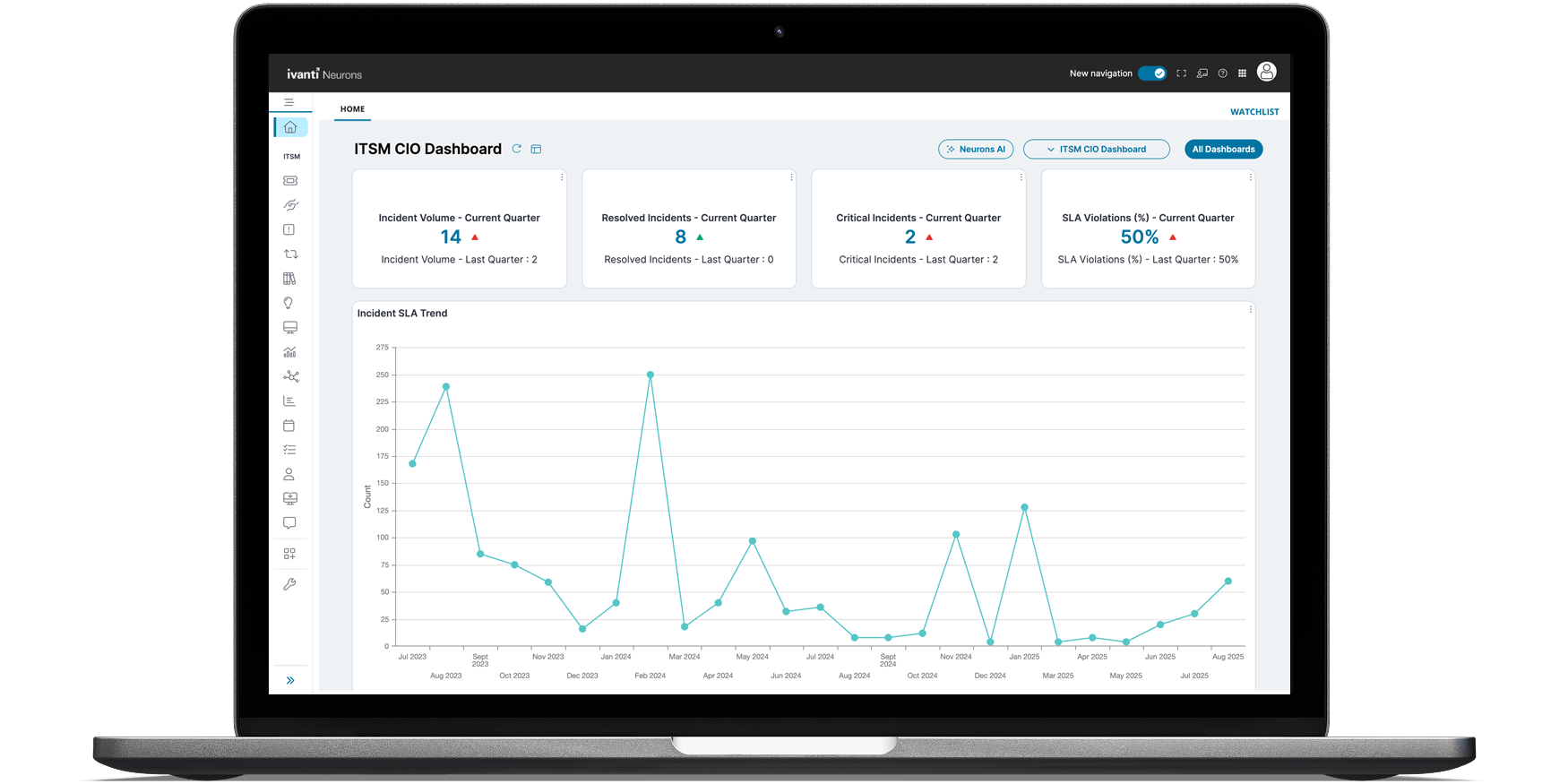
Security teams can audit every Endpoint action taken, while gaining visibility into where AI tools, models and services are running across developer systems. It also provides enforcement rules and policies by team, role and device. The goal is to replace rigid, organization-wide rules with controls designed for real-world use.
The company said that its threat intelligence software protects against more than 100,000 weekly threats and that supply chain attacks are on the rise, especially with insecure npm packages.
A supply chain attacks a cyberattack in which cybercriminals compromise a trusted vendor, software package or service to gain access to organizations or users who depend on it. Recent articles have become the bellwether of this trend, including interrupting the Axios JavaScript library late last month.
Image: SiliconANGLE/Microsoft Designer
Support our mission to keep content open and free by engaging with the CUBE community. Join CUBE’s Alumni Trust Networkwhere technology leaders connect, share wisdom and create opportunities.
- 15M+ viewers of CUBE videosenabling conversations across AI, cloud, cybersecurity and more
- 11.4k+ CUBE alumni – Connect with more than 11,400 technology and business leaders who are shaping the future through a unique network based on trust.
About SiliconANGLE Media
Founded by technology visionaries John Furrier and Dave Vellante, SiliconANGLE Media has built a dynamic ecosystem of industry-leading digital media products that reach 15+ million elite technology professionals. Our new ownership of CUBE AI Video Cloud is starting to engage with audiences, using CUBEai.com’s neural network to help technology companies make data-driven decisions and stay at the forefront of industry conversations.