CISA advises bidders to exploit Ivanti EPMM error on Sunday

CISA has given US government agencies four days to protect their systems from the most vulnerable Ivanti Endpoint Manager Mobile (EPMM) that has been exploited in attacks since January.
Tracked as CVE-2026-1340, this critical code injection flaw enables unprivileged threat actors to obtain remote code execution on exposed and unpublished EPMM appliances.
Ivanti flagged this and a second security bug (CVE-2026-1281) as being exploited in a zero-day attack when it released security updates on January 29 to close both vulnerabilities and “strongly” encouraged all customers to update their systems to prevent further exploits.

“A successful exploit could lead to unauthorized remote code execution. We are aware of a very limited number of customers whose solution was in use at the time of the disclosure,” the company said at the time.
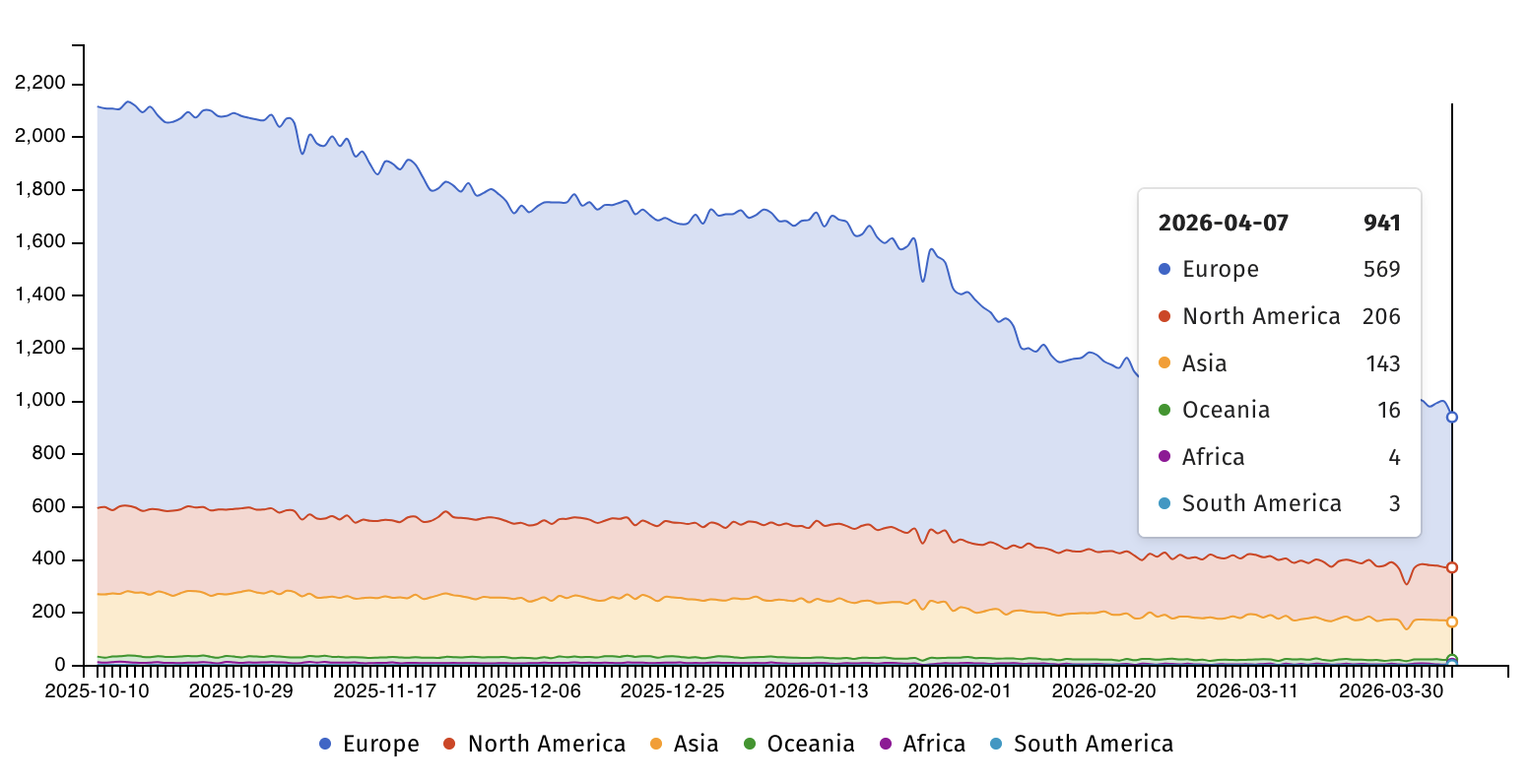
Internet security watchdog group Shadowserver is currently tracking nearly 950 IP addresses and fingerprints of Ivanti EPMM exposed on the Internet, most of them from Europe (569) and North America (206). However, there is no information on how many of them have already been released.
On Monday, the Cybersecurity and Infrastructure Security Agency of the US added a vulnerability to its catalog known as Known Exploited Vulnerabilities (KEV) and ordered the Federal Civilian Executive Branch (FCEB) to install their EPMM systems on Saturday midnight, April 11, as ordered by the Binding Operational Directive (BOD22-01).
“This type of vulnerability is a common attack by malicious actors and poses a significant risk to government business,” CISA warned. “Use mitigations in each vendor’s instructions, follow applicable BOD 22-01 guidelines for cloud services, or stop using the product if mitigations are not available.”
CISA advised all security guards, including those in the private sector, to prioritize applying CVE-2026-1340 to secure their organizations’ devices as soon as possible, although BOD 22-01 only applies to US government agencies.
Some of Ivanti’s vulnerabilities have been exploited in recent years with zero-day attacks to breach multiple targets, including government agencies around the world.
In total, CISA flagged 33 Ivanti vulnerabilities as being exploited in the attack, 12 of which were used in various ransomware operations.
Ivanti provides IT asset management products to more than 40,000 customers through a network of more than 7,000 partners worldwide.

Automatic logging proves that the path exists. BAS proves that your controls are stopping you. Many teams run without each other.
This white paper outlines six areas of validation, indicates where coverage ends, and provides clinicians with three diagnostic questions for any screening tool.