Critical Nginx UI auth bypass flaw is now being actively exploited in the wild

A critical vulnerability in Nginx UI with Model Context Protocol (MCP) support is now being exploited in the wild for full server hijacking without authentication.
The flaw, tracked as CVE-2026-33032, is caused by nginx-ui leaving the ‘/mcp_message’ endpoint unprotected, allowing remote attackers to request privileged MCP actions without credentials.
Because those actions include writing and reloading nginx configuration files, a single unauthorized request can change server behavior and effectively take over a web server.

“[…] any network attacker can request all MCP tools without authentication, including restarting nginx, creating/modifying/deleting nginx configuration files, and triggering automatic reloads – achieving complete nginx service takeover,” reads NIST’s description of the flaw in the National Vulnerability Database (NVD).
NGNIX released a bug fix in version 2.3.4 on March 15, a day after researchers at AI workflow security company Pluto Security AI reported it. However, the vulnerability identifier, along with technical details and a proof-of-concept (PoC), appeared at the end of the month.
In a CVE Landscape report earlier this week, threat intelligence firm Record Future notes that CVE-2026-33032 is subject to an active exploit.
Nginx UI is a web-based administration interface for the Nginx web server. The library is very popular, with over 11,000 stars on GitHub and 430,000 Docker pulls.
Based on Pluto Security’s online testing using the Shodan engine, there are currently 2,600 publicly exposed instances that are vulnerable to attack. Most are in China, the United States, Indonesia, Germany and Hong Kong.
In today’s report, Yotam Perkal of Pluto Security states that the exploit only requires network access and is achieved by establishing an SSE connection, opening an MCP session, and then using the returned ‘sessionID’ to send requests to the ‘/mcp_message’ endpoint.
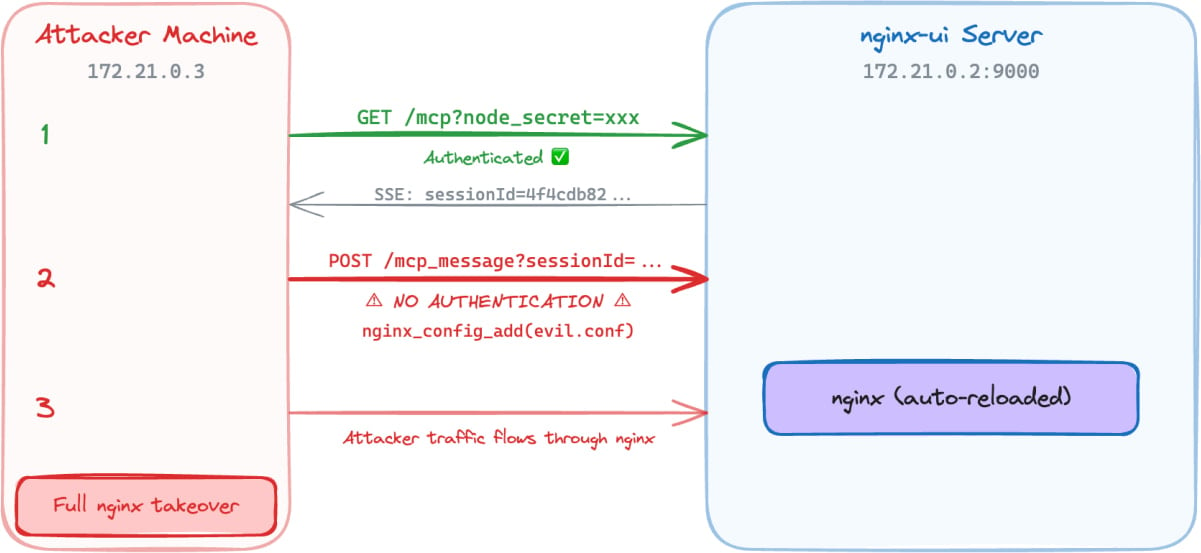
Source: Pluto Security
From there, attackers can request MCP tools without authentication and take the following steps:
- Connect to the target nginx-ui instance
- Send requests without any confirmation headers
- Gain access to all 12 MCP tools (7 damage)
- Read the nginx configuration files and extract them
- Install a new nginx server block with malicious configuration
- Enable automatic nginx reload
The Pluto Security demo shows that an attacker can use an unauthorized MCP message endpoint to perform privileged nginx administrative actions, perform configuration injection, and ultimately take control of an nginx server, all without authentication.
Given the nature of active exploits and the existence of public PoCs, system administrators are recommended to apply available security updates as soon as possible. The latest secure version of nginx-ui is 2.3.6, released last week.

Automatic logging proves that the path exists. BAS proves that your controls are stopping you. Many teams run without each other.
This white paper outlines six areas of validation, indicates where coverage ends, and provides clinicians with three diagnostic questions for any screening tool.