The Bitwarden CLI npm package is vulnerable to developer identity theft

Updated with additional information from Bitwarden.
The Bitwarden CLI was temporarily compromised after attackers uploaded a malicious @bitwarden/cli package to npm that contained a data-stealing payload that could spread to other projects.
According to reports by Socket, JFrog, and OX Security, the malicious package was distributed as version 2026.4.0 and remained available between 5:57 PM and 7:30 PM ET on April 22, 2026, before it was removed.

Bitwarden confirmed the incident, saying the breach only affected its npm distribution channel for the CLI npm package and those who downloaded the malicious version.
“The investigation found no evidence that the user’s vault data was ultimately accessed or compromised, or that production data or production systems were compromised. Once the problem was discovered, the vulnerability was revoked, the malicious npm release was revoked, and corrective actions were immediately initiated,” Bitwarden shared in a statement.
“The problem affected npm’s CLI distribution mechanism during that limited window, not the integrity of the official Bitwarden CLI codebase or the stored vault data.”
Bitwarden says it has revoked access to the vulnerability and downgraded the affected CLI npm release.
Bitwarden supply chain attack
According to Socket, malicious actors appear to have used GitHub’s deprecated action in Bitwarden’s CI/CD pipeline to inject malicious code into the CLI npm package.
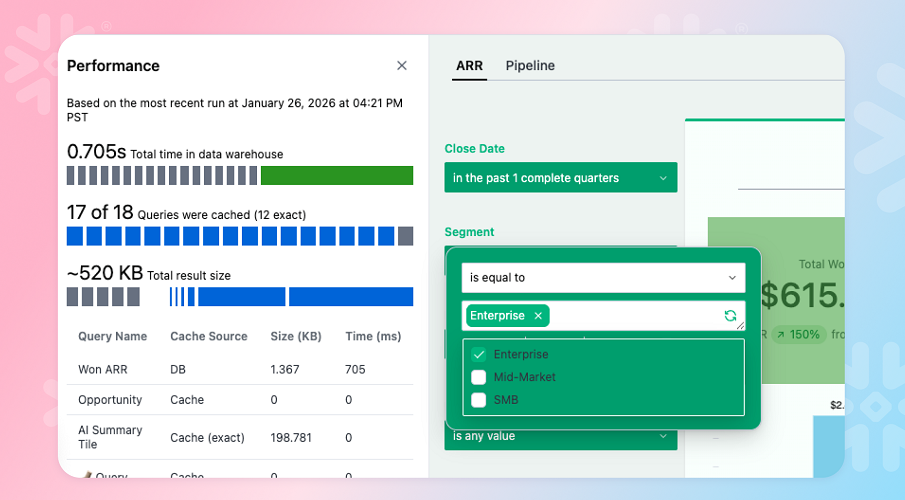
According to JFrog, this package has been modified so that the install script and CLI entry point use a custom named loader. bw_setup.jswhich checks for the Bun runtime and, if it doesn’t exist, downloads it.
The loader then uses the Bun runtime to launch the named obfuscated JavaScript file bw1.jswhich acts as a malware to steal information.
Source: Jfrog
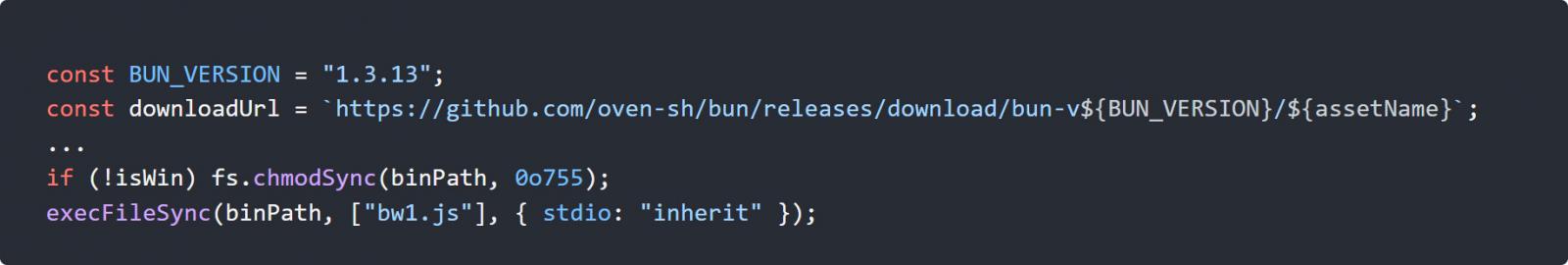
Once released, the malware collects a bunch of secrets from infected systems, including npm tokens, GitHub authentication tokens, SSH keys, and AWS, Azure, and Google Cloud cloud credentials.
The malware encrypts the collected data using AES-256-GCM and releases it by creating public GitHub repositories under the victim’s account, where the encrypted data is stored.
OX Security says the repositories it created contain the string “Shai-Hulud: The Third Coming,” a reference to a previous npm supply chain attack that used the same method as a text string when extracting stolen data.
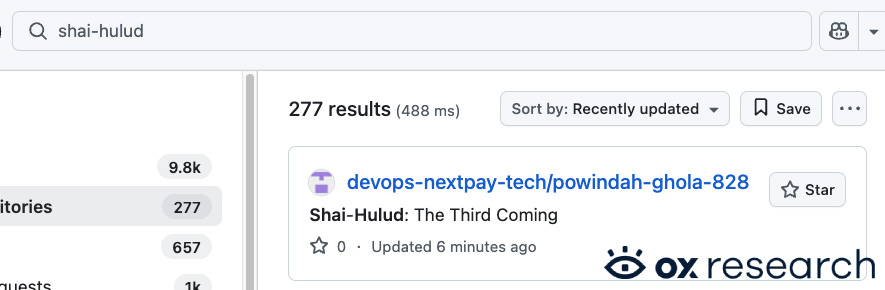
Source: OX Security
The malware also includes self-casting capabilities, and OX Security reports that it can use stolen npm credentials to identify packages that a victim can modify and inject with malicious code.
Socket also realized that the payload was targeting CI/CD environments and attempts to harvest secrets that could be reused to augment the attack.
The attack comes after Checkmarx disclosed a separate procurement incident yesterday affecting its KICS Docker images, GitHub Actions, and developer extensions.
While it’s not known exactly how the attackers gained access, Bitwarden told BleepingComputer that the incident was linked to an attack on the Checkmarx supply chain, with a Checkmarx-related development tool that was vulnerable allowing abuse of the npm CLI delivery method during a limited window.
Socket told BleepingComputer that there is some overlap between the Checkmarx breach and this attack.
“The connection is at the level of malware and infrastructure. In the case of Bitwarden, the malicious payload uses the same audit.checkmarx[.]cx/v1/telemetry conclusion from the Checkmarx event. It also uses the same __decodeScrambled obfuscation principle and seeds 0x3039and shows the same common pattern of identity theft, GitHub-based divestment, and supply chain distribution behavior,” Socket told BleepingComputer.
“That overlap goes beyond superficial similarities. Bitwarden’s payload contains the same kind of embedded gzip+base64 components we’ve seen in previous malware, including the use of evidence gathering and downstream exploits.”
Both campaigns have been linked to a malicious actor known as TeamPCP, which previously targeted developer packages for major Trivy and LiteLLM attacks.
Developers who have installed the affected version should treat their systems and credentials as vulnerable and rotate all exposed credentials, especially those used for CI/CD pipelines, cloud storage, and developer environments.
Update 4/23/26: Updated the story with information from Bitwarden confirming that the incident is related to the Checkmarx supply chain attack.

AI has tied four zero days to a single exploit that bypasses both renderer and OS sandboxes. A wave of new exploits is coming.
At the Automated Validation Conference (May 12 & 14), see how autonomous, context-rich validation finds usability, validates controls, and closes the correction loop.
Find Your Place